|
|
Post by nanadeb on Jan 21, 2015 16:08:29 GMT -8
Wow - I'm glad to hear I'm not the only one. Thank you so much for continuing to help me with this, Quads!
|
|
Quads
Malware Removalists
In New Zealand
Posts: 9,387
|
Post by Quads on Jan 21, 2015 18:43:18 GMT -8
You do still have FRST on the Flash Drive just in case as it looks like we are dealing with
C:\DOCUME~1\User\LOCALS~1\Temp\tmp[Numbers].tmp
C:\DOCUME~1\User\LOCALS~1\Temp\NTFS.sys
C:\DOCUME~1\User\LOCALS~1\Temp\tmp[Numbers].tmp
PHYSICALDRIVE0 <<<<=================== We are talking Boot Sector from here and below
C:\Device\Harddisk0\Partition0
C:\Device\Harddisk0\Partition1
Due to the deeper level and trying to deal with it things can go wrong, and FRST can be used to log and fix non booting Windows from Flash Drive. BUT I would say to carefully copy of personal docs, photo's etc so you have the backup of personal files.
Quads
|
|
|
|
Post by nanadeb on Jan 22, 2015 4:54:15 GMT -8
Ok - copied FRST to flash and personal pics - I never keep any important docs on this computer. I'm headed to my office so won't be able to work on this until around 6pm EST today. Look forward to your next instruction.
|
|
Quads
Malware Removalists
In New Zealand
Posts: 9,387
|
Post by Quads on Jan 22, 2015 9:37:25 GMT -8
|
|
|
|
Post by nanadeb on Jan 22, 2015 17:55:02 GMT -8
*Sigh*
Downloaded but unable to open or run, even run as administrator - no response, no security warning window.
|
|
Quads
Malware Removalists
In New Zealand
Posts: 9,387
|
Post by Quads on Jan 22, 2015 18:06:50 GMT -8
Hmmmm getting there, people who created (up keep the tools have also been notified) Thinking.
Quads
|
|
Quads
Malware Removalists
In New Zealand
Posts: 9,387
|
Post by Quads on Jan 22, 2015 18:53:38 GMT -8
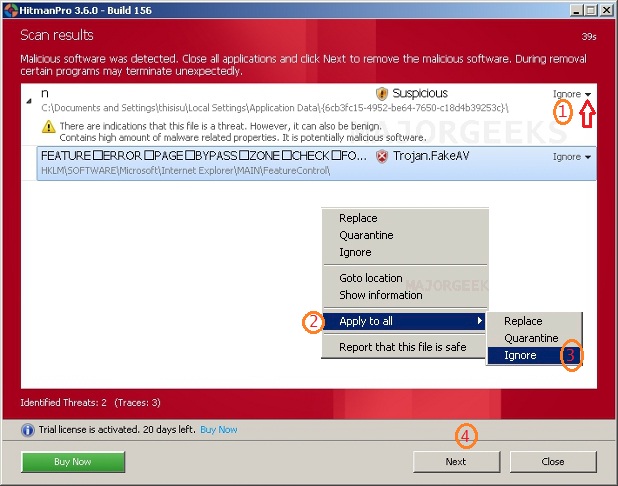
HitmaPro NOTE THE INSTRUCTION BELOW SO THAT IT WON"T ATTEMPT TO FIX ANYTHING AS I JUT WANT SOMETHING TO CONFIRM WHAT IT IS!!!!1. Download HitmanPro 64 Bit dl.surfright.nl/HitmanPro_x64.exe2.Launch the program by double clicking on the  icon. (Windows Vista/7 users right click on the HitmanPro icon and select run as administrator).
Note: If the program won't run please then open the program while holding down the left CTRL key until the program is loaded.
3.Click on the next button. You must agree with the terms of EULA. (if asked) 4.Check the box beside "No, I only want to perform a one-time scan to check this computer".
5.Click on the next button. 6.The program will start to scan the computer. 7.When the scan is done click on drop-down menu of the found entries (if any) and choose - Apply to all => Ignore <= IMPORTANT!!!
 8.Click on the next button. 9.Click on the " Save Log" button. 10.Save that file to your desktop and post the content of that file in your next reply. Note: if there isn't a dropdown menu when the scan is done then please don't delete anything and close HitmanPro Other log location, Navigate to C :\Documents and Settings\All Users\Application Data\HitmanPro\Logs open the report and copy and paste it to your next reply. Quads |
|
|
|
Post by nanadeb on Jan 23, 2015 12:18:47 GMT -8
No threats found - so weird. Opened and ran without issue though.
Here is the log.
HitmanPro 3.7.9.234
www.hitmanpro.com
Computer name . . . . : DEB-HP
Windows . . . . . . . : 6.1.1.7601.X64/2
User name . . . . . . : Deb-HP\Safe Mode
UAC . . . . . . . . . : Disabled
License . . . . . . . : Free
Scan date . . . . . . : 2015-01-23 15:02:04
Scan mode . . . . . . : Normal
Scan duration . . . . : 11m 28s
Disk access mode . . : Direct disk access (SRB)
Cloud . . . . . . . . : Internet
Reboot . . . . . . . : No
Threats . . . . . . . : 0
Traces . . . . . . . : 48
Objects scanned . . . : 5,101,035
Files scanned . . . . : 688,960
Remnants scanned . . : 3,382,084 files / 1,029,991 keys
Malware _____________________________________________________________________
Volume Boot Record (Sector 2048)
C:$VBR_2048
Suspicious files ____________________________________________________________
C:\Users\Safe Mode\Desktop\explorer.exe.exe
Size . . . . . . . : 2,126,848 bytes
Age . . . . . . . : 3.8 days (2015-01-19 20:38:46)
Entropy . . . . . : 7.5
SHA-256 . . . . . : 4197EA9100675E349849D13ED144F9E88E0039DAEBB6D2DB343A3E424CA79CD9
Needs elevation . : Yes
Fuzzy . . . . . . : 24.0
Program has no publisher information but prompts the user for permission elevation.
Entropy (or randomness) indicates the program is encrypted, compressed or obfuscated. This is not typical for most programs.
Authors name is missing in version info. This is not common to most programs.
Version control is missing. This file is probably created by an individual. This is not typical for most programs.
Time indicates that the file appeared recently on this computer.
Forensic Cluster
0.0s C:\Users\Safe Mode\Desktop\explorer.exe.exe
0.1s C:\ProgramData\Microsoft\Search\Data\Applications\Windows\Projects\SystemIndex\Indexer\CiFiles\00010004.wid
0.1s C:\ProgramData\Microsoft\Search\Data\Applications\Windows\Projects\SystemIndex\Indexer\CiFiles\00010004.ci
0.3s C:\ProgramData\Microsoft\Search\Data\Applications\Windows\Projects\SystemIndex\Indexer\CiFiles\00010004.dir
Potential Unwanted Programs _________________________________________________
ask.com
C:\Users\Deb\AppData\Local\Google\Chrome\User Data\Default\Web Data
ask.com_
C:\Users\Deb\AppData\Local\Google\Chrome\User Data\Default\Web Data
C:\Users\Deb\AppData\Roaming\OpenCandy\ (Conduit)
Cookies _____________________________________________________________________
C:\Users\Deb\AppData\Local\Google\Chrome\User Data\Default\Cookies:ad.360yield.com
C:\Users\Deb\AppData\Local\Google\Chrome\User Data\Default\Cookies:ad.mlnadvertising.com
C:\Users\Deb\AppData\Local\Google\Chrome\User Data\Default\Cookies:ads.pubmatic.com
C:\Users\Deb\AppData\Local\Google\Chrome\User Data\Default\Cookies:adtechus.com
C:\Users\Deb\AppData\Local\Google\Chrome\User Data\Default\Cookies:burstnet.com
C:\Users\Deb\AppData\Local\Google\Chrome\User Data\Default\Cookies:casalemedia.com
C:\Users\Deb\AppData\Local\Google\Chrome\User Data\Default\Cookies:doubleclick.net
C:\Users\Deb\AppData\Local\Google\Chrome\User Data\Default\Cookies:interclick.com
C:\Users\Deb\AppData\Local\Google\Chrome\User Data\Default\Cookies:media6degrees.com
C:\Users\Deb\AppData\Local\Google\Chrome\User Data\Default\Cookies:revsci.net
C:\Users\Deb\AppData\Local\Google\Chrome\User Data\Default\Cookies:ru4.com
C:\Users\Deb\AppData\Local\Google\Chrome\User Data\Default\Cookies:serving-sys.com
C:\Users\Deb\AppData\Local\Google\Chrome\User Data\Default\Cookies:www.googleadservices.com
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\0MZORLCF.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\140JMA5J.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\1ETQDETK.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\4FU0YR7P.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\4G1Q3WG1.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\53N2WKHW.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\5FC53MVG.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\5IVQ6RP1.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\5N8ES3N7.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\71LWFAG8.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\790WSZSG.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\7DB2MSCG.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\AH8VAP2U.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\AT5UAY3H.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\BRI7R2DC.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\BXFLAHOV.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\CRVSSO29.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\DYXD60WD.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\EP7XT3FI.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\ERPM5BGS.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\GOTAU73J.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\M4FE601U.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\MY05648R.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\NMJWUP7H.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\OE727X45.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\OTGJ8MHO.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\QLXAHBGK.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\STWKHPNW.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\TT67EQMK.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\WEHMQI8H.txt
C:\Users\Safe Mode\AppData\Roaming\Microsoft\Windows\Cookies\XJK4O0Z4.txt
|
|
Quads
Malware Removalists
In New Zealand
Posts: 9,387
|
Post by Quads on Jan 23, 2015 14:33:13 GMT -8
Ok if you look carefully listed is
Malware _____________________________________________________________________
Volume Boot Record (Sector 2048)
C:$VBR_2048
Quads
|
|
|
|
Post by nanadeb on Jan 23, 2015 14:42:59 GMT -8
Oh yes - totally missed that! I will await your next instruct  |
|