dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Oct 25, 2016 20:39:09 GMT -8
Lot to do here; let's get started .... FIRST >>>>Did you know that System Restore is disabled? If you did not do this intentionally, please check the following: Go to Start and type System in the search box. Click on System (under Control Panel or Settings) and then on System Protection. Click on Configure and then select Turn on system protection. Click Apply and then OK. In the System Protection screen, is Protection now On for the drive? SECOND >>>>Open notepad by pressing the Windows Key + R key, typing notepad in the Run box and pressing Enter. Please copy the contents of the quote box below. To do this highlight the contents of the box and right click on it and select copy. Paste this into the open notepad. Save it to your desktop as fixlist.txtNOTE. It's important that both files, FRST64 and fixlist.txt are in the same location or the fix will not work. NOTICE: This script was written specifically for this user, for use on that particular machine. Running this on another machine may cause damage to your operating systemStart FRST that is on the desktop by right clicking on file and selecting "Run as Administrator..." and press the Fix button just once and wait.  If for some reason the tool needs a restart, please make sure you let the system restart normally. After that let the tool complete its run. When finished FRST will generate a log on the Desktop (Fixlog.txt). Please post it to your reply. LAST >>>>INFO TO REPLY WITH:How is your system running now? How did the System Restore 'fix' go? The Fixlog.txt text file (you should be able to attach this file; no need for wikisend.com usually). Any questions you have? |
|
|
|
Post by sasha22 on Oct 26, 2016 6:24:04 GMT -8
Fixlog.txt (214.45 KB)
The fix went well. I have had my system on for about 5 hours and no Norton's popup saying the Trojan.kotver!gm2 was found and to restart pc to complete the removal. So, it appears to be fixed. Thank you so much. Is there something I can do so that I won't get this again? Should I now delete all the files I created for this issue? i.e. FRST64.exe, FRST.txt, addition.txt, and fixlog.txt
Also, my system did no show that the System Restore was disabled. I did find under Disk Space Usage to be set at a max usage of 1% (9.17gb) I have changed this to 30% (275.22gb) What should (or is the best) this be set at? |
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Oct 27, 2016 7:43:45 GMT -8
That's good news about Norton not finding Kotver any more; yes, it looks like the script file removed the malware. That is strange about System Restore; the log showed some abnormalities about the service but that could have been just the scanner itself. I do this work on my own time and it is 'volunteered' time. Sorry for taking so long to reply but I had some issues with my own system yesterday. As to other help, I offer what I can and can recommend other good forums if the issue is beyond my comfort level but mainly I now focus on fighting malware. All questions are welcome however.
Let's get a close look for any left overs .... FIRST >>>>Junkware Removal ToolPlease download JRT from here to your desktop. Note: Temporarily disable/shut down your protection software now to avoid potential conflicts, how to do so can be read here.Double click the JRT.exe file to run the application. The application will open an Command Prompt window and run from there (this is normal for this program, so not to be alarmed). When it is asked, press any key to allow the program to continue / run. This will create a log on the desktop; please copy and paste the JRT.txt log text in your next post. Note: After the log file is created, please enable your protection software / reboot your system and verify your protection software is enabled.SECOND >>>>AdwCleaner by XplodeDownload AdwCleaner from here or from here. Save the file to the desktop. NOTE: If you are using IE 8 or above you may get a warning that stops the program from downloading. Just click on the warning and allow the download to complete. Close all open windows and browsers.Vista/7/8 users: Right click the AdwCleaner icon on the desktop, click Run as administrator and accept the UAC prompt to run AdwCleaner. You will see the following console:  Click the Scan button and wait for the scan to finish. After the Scan has finished the window may or may not show what it found and above, in the progress bar, you will see: Waiting for action. Please uncheck elements you don't want to remove.Click the Clean button. Everything checked will be deleted. When the program has finished cleaning a report appears. Once done it will ask to reboot, allow this 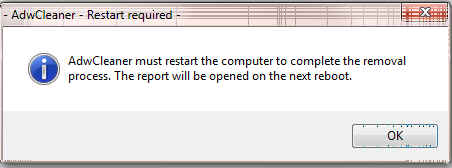 On reboot a log will be produced please copy / paste that in your next reply. This report is also saved to C:\AdwCleaner\AdwCleaner[C#].txtOptional: NOTE: If you see AVG Secure Search being targeted for deletion, Here's Why and Here. You can always Reinstall it. LAST >>>>Malwarebytes' Anti-MalwarePlease download the latest version of Malwarebytes' Anti-Malware from Here. Double Click on the mbam-setup.exe file to install the application. Make sure a checkmark is placed next to Update Malwarebytes' Anti-Malware and Launch Malwarebytes' Anti-Malware, then click Finish. If an update is found, it will download and install the latest version. When the main screen opens, if the database is out of date, you can click on the Fix Now banner or the Update Now link  Once the program has loaded and updated, select " Scan Now >>" to start the scan.  The scan may take some time to finish, so please be patient. If any malware is found, you will be presented with a screen like the one below.  If any malware is found, make sure that everything is checked, and click Remove Selected. When the scan is complete, click View detailed log >> to view the results. The report screen will open. At the bottom click on Export and select as txt file, save the file to your desktop and click OK. When the export is complete, select OPEN. The log file will be opened in your default text file viewer (usually Notepad); select the whole text (Ctrl + A) and copy (Ctrl + c) it to paste here in a reply. |
|
|
|
Post by sasha22 on Oct 29, 2016 7:42:23 GMT -8
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Junkware Removal Tool (JRT) by Malwarebytes
Version: 8.0.9 (09.30.2016)
Operating System: Windows 7 Home Premium x64
Ran by Sasha22 (Administrator) on Sat 10/29/2016 at 9:58:30.63
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
File System: 32
Failed to delete: C:\Users\Sasha22\AppData\Local\tempdir (Folder)
Successfully deleted: C:\ProgramData\alawar (Folder)
Successfully deleted: C:\ProgramData\alawarwrapper (Folder)
Successfully deleted: C:\ProgramData\partner (Folder)
Successfully deleted: C:\ProgramData\trymedia (Folder)
Successfully deleted: C:\users\Public\Documents\alawarwrapper (Folder)
Successfully deleted: C:\users\Public\Documents\downloaded installers (Folder)
Successfully deleted: C:\Users\Sasha22\AppData\Local\alawarwrapper (Folder)
Successfully deleted: C:\Users\Sasha22\AppData\Local\packageaware (Folder)
Successfully deleted: C:\Users\Sasha22\AppData\Local\slimware utilities inc (Folder)
Successfully deleted: C:\Users\Sasha22\Appdata\LocalLow\bfgbar (Folder)
Successfully deleted: C:\Users\Sasha22\Appdata\LocalLow\conduit (Folder)
Successfully deleted: C:\Users\Sasha22\AppData\Roaming\alawar (Folder)
Successfully deleted: C:\Users\Sasha22\AppData\Roaming\alawarentertainment (Folder)
Successfully deleted: C:\Users\Sasha22\AppData\Roaming\iwin (Folder)
Successfully deleted: C:\Users\Sasha22\AppData\Roaming\Mozilla\Firefox\Profiles\components\yahoo-search.xml (File)
Successfully deleted: C:\Users\Sasha22\AppData\Roaming\registry mechanic (Folder)
Successfully deleted: C:\Windows\reimage.ini (File)
Successfully deleted: C:\Windows\Tasks\BeFrugal.com Toolbar.job (Task)
Successfully deleted: C:\Windows\wininit.ini (File)
Successfully deleted: C:\Program Files (x86)\bfgbar (Folder)
Successfully deleted: C:\Program Files (x86)\driverupdate (Folder)
Successfully deleted: C:\Program Files (x86)\gamingwonderlandei (Folder)
Successfully deleted: C:\Users\Sasha22\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0EEVTZJP (Temporary Internet Files Folder)
Successfully deleted: C:\Users\Sasha22\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0WO0O62J (Temporary Internet Files Folder)
Successfully deleted: C:\Users\Sasha22\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\2ZRGOZE7 (Temporary Internet Files Folder)
Successfully deleted: C:\Users\Sasha22\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H7EOH612 (Temporary Internet Files Folder)
Successfully deleted: C:\Windows\prefetch\COUPONS.COMTOOLBARHELPER.EXE-D578233D.pf (File)
Successfully deleted: C:\Windows\System32\config\systemprofile\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0EEVTZJP (Temporary Internet Files Folder)
Successfully deleted: C:\Windows\System32\config\systemprofile\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0WO0O62J (Temporary Internet Files Folder)
Successfully deleted: C:\Windows\System32\config\systemprofile\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\2ZRGOZE7 (Temporary Internet Files Folder)
Successfully deleted: C:\Windows\System32\config\systemprofile\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H7EOH612 (Temporary Internet Files Folder)
Registry: 1
Successfully deleted: HKCU\Software\Microsoft\Internet Explorer\SearchScopes\{AFBCB7E0-F91A-4951-9F31-58FEE57A25C4} (Registry Key)
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Scan was completed on Sat 10/29/2016 at 10:02:01.45
End of JRT log
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
# AdwCleaner v6.030 - Logfile created 29/10/2016 at 10:37:04
# Updated on 19/10/2016 by Malwarebytes
# Database : 2016-10-28.2 [Server]
# Operating System : Windows 7 Home Premium Service Pack 1 (X64)
# Username : Sasha22 - SASHA22-PC
# Running from : C:\Users\Sasha22\Desktop\adwcleaner_6.030.exe
# Mode: Clean
# Support : hxxps://www.malwarebytes.com/support
***** [ Services ] *****
***** [ Folders ] *****
[-] Folder deleted: C:\Users\Sasha22\AppData\LocalLow\HPAppData
[-] Folder deleted: C:\Users\Sasha22\AppData\LocalLow\Yahoo!\Companion
[-] Folder deleted: C:\Users\Sasha22\AppData\Roaming\quickclick
[-] Folder deleted: C:\Users\Sasha22\AppData\Roaming\Yahoo!\Companion
[-] Folder deleted: C:\Users\Sasha22\AppData\Roaming\Pogo Games
[-] Folder deleted: C:\ProgramData\quickclick
[#] Folder deleted on reboot: C:\ProgramData\Application Data\quickclick
[-] Folder deleted: C:\Users\Public\Documents\iWin
***** [ Files ] *****
[-] File deleted: C:\Users\Sasha22\AppData\LocalLow\Microsoft\Internet Explorer\Services\Search_ask.com.xml
***** [ DLL ] *****
***** [ WMI ] *****
***** [ Shortcuts ] *****
***** [ Scheduled Tasks ] *****
***** [ Registry ] *****
[-] Key deleted: HKLM\SOFTWARE\Classes\Toolbar.CT2559647
[-] Key deleted: HKCU\Software\Microsoft\Internet Explorer\DOMStorage\gamingwonderland.com
[-] Key deleted: HKCU\Software\Microsoft\Internet Explorer\DOMStorage\myway.com
[-] Key deleted: HKCU\Software\Microsoft\Internet Explorer\DOMStorage\mywebface.com
[-] Key deleted: HKLM\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{31bb1be0-1fc3-4279-a659-2b3ea16bc7ca}
[-] Key deleted: HKLM\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{82024f98-f9fb-47f4-860f-887e41883c9d}
[-] Key deleted: HKLM\SOFTWARE\Classes\YBrowserToolbar.YBrowserToolbar
[-] Key deleted: HKLM\SOFTWARE\Classes\YBrowserToolbar.YBrowserToolbar.1
[#] Key deleted on reboot: [x64] HKLM\SOFTWARE\Classes\YBrowserToolbar.YBrowserToolbar
[#] Key deleted on reboot: [x64] HKLM\SOFTWARE\Classes\YBrowserToolbar.YBrowserToolbar.1
[-] Key deleted: HKLM\SOFTWARE\Classes\AppID\{28FF42B8-A0DA-4BE5-9B81-E26DD59B350A}
[-] Key deleted: HKLM\SOFTWARE\Classes\AppID\{7D831388-D405-4272-9511-A07440AD2927}
[-] Key deleted: HKLM\SOFTWARE\Classes\CLSID\{3BF72F68-72D8-461D-A884-329D936C5581}
[-] Key deleted: HKLM\SOFTWARE\Classes\CLSID\{78E9D883-93CD-4072-BEF3-38EE581E2839}
[-] Key deleted: HKLM\SOFTWARE\Classes\CLSID\{83AC1413-FCE4-4A46-9DD5-4F31F306E71F}
[-] Key deleted: HKLM\SOFTWARE\Classes\CLSID\{DE9028D0-5FFA-4E69-94E3-89EE8741F468}
[-] Key deleted: HKLM\SOFTWARE\Classes\CLSID\{E7DF6BFF-55A5-4EB7-A673-4ED3E9456D39}
[-] Key deleted: HKLM\SOFTWARE\Classes\CLSID\{5D637FAD-E202-48D1-8F18-5B9C459BD1E3}
[-] Key deleted: HKLM\SOFTWARE\Classes\CLSID\{F51C15D4-3D0A-4DBA-A095-EBCC09F24DA2}
[-] Key deleted: HKLM\SOFTWARE\Classes\Interface\{03E2A1F3-4402-4121-8B35-733216D61217}
[-] Key deleted: HKLM\SOFTWARE\Classes\Interface\{9E3B11F6-4179-4603-A71B-A55F4BCB0BEC}
[-] Key deleted: HKLM\SOFTWARE\Classes\Interface\{9BB31AD8-5DB2-459E-A901-DEA536F23BA4}
[-] Key deleted: HKLM\SOFTWARE\Classes\Interface\{BD51A48E-EB5F-4454-8774-EF962DF64546}
[-] Key deleted: HKLM\SOFTWARE\Classes\Interface\{8233093C-178B-484B-979E-3C6B5B147DBC}
[-] Key deleted: HKLM\SOFTWARE\Classes\TypeLib\{9C049BA6-EA47-4AC3-AED6-A66D8DC9E1D8}
[-] Key deleted: HKLM\SOFTWARE\Classes\TypeLib\{C4C4F1F4-3074-4CB6-9FB8-0A64273166F0}
[-] Key deleted: HKLM\SOFTWARE\Classes\TypeLib\{FA6468D2-FAA4-4951-A53B-2A5CF9CC0A36}
[-] Key deleted: HKLM\SOFTWARE\Classes\TypeLib\{B722ED8B-0B38-408E-BB89-260C73BCF3D4}
[-] Key deleted: HKLM\SOFTWARE\Microsoft\Code Store Database\Distribution Units\{5D637FAD-E202-48D1-8F18-5B9C459BD1E3}
[-] Key deleted: HKCU\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{AB6BD08C-DB6B-4F02-8A22-4BD343E990FF}
[-] Key deleted: HKCU\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{F25AF245-4A81-40DC-92F9-E9021F207706}
[-] Key deleted: HKCU\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{AB5D199E-9659-47A2-930B-FC3B69061353}
[-] Key deleted: HKCU\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{5D637FAD-E202-48D1-8F18-5B9C459BD1E3}
[-] Key deleted: HKCU\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{9522B3FB-7A2B-4646-8AF6-36E7F593073C}
[-] Key deleted: HKCU\Software\Microsoft\Windows\CurrentVersion\Ext\Settings\{AB6BD08C-DB6B-4F02-8A22-4BD343E990FF}
[-] Key deleted: HKCU\Software\Microsoft\Windows\CurrentVersion\Ext\Settings\{F25AF245-4A81-40DC-92F9-E9021F207706}
[-] Key deleted: HKCU\Software\Microsoft\Windows\CurrentVersion\Ext\Settings\{AB5D199E-9659-47A2-930B-FC3B69061353}
[-] Key deleted: HKCU\Software\Microsoft\Windows\CurrentVersion\Ext\Settings\{5D637FAD-E202-48D1-8F18-5B9C459BD1E3}
[-] Key deleted: HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Ext\PreApproved\{02478D38-C3F9-4EFB-9B51-7695ECA05670}
[-] Key deleted: HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Ext\PreApproved\{EF99BD32-C1FB-11D2-892F-0090271D4F88}
[-] Key deleted: HKLM\SOFTWARE\Microsoft\Internet Explorer\ActiveX Compatibility\{9522B3FB-7A2B-4646-8AF6-36E7F593073C}
[-] Key deleted: HKU\S-1-5-21-2287122347-3831853411-1151728686-1001\Software\BEFRUGAL
[-] Key deleted: HKU\S-1-5-21-2287122347-3831853411-1151728686-1001\Software\Reimage
[-] Key deleted: HKU\S-1-5-21-2287122347-3831853411-1151728686-1001\Software\SlimWare Utilities Inc
[-] Key deleted: HKU\S-1-5-21-2287122347-3831853411-1151728686-1001\Software\Yahoo\Companion
[-] Key deleted: HKU\S-1-5-21-2287122347-3831853411-1151728686-1001\Software\Yahoo\YFriendsBar
[-] Key deleted: HKU\S-1-5-21-2287122347-3831853411-1151728686-1001\Software\YahooPartnerToolbar
[-] Key deleted: HKU\S-1-5-21-2287122347-3831853411-1151728686-1001\Software\Local AppWizard-Generated Applications\Reimage - Windows Problem Relief.
[-] Key deleted: HKU\S-1-5-21-2287122347-3831853411-1151728686-1001\Software\AppDataLow\Software\ConduitSearchScopes
[-] Key deleted: HKU\S-1-5-21-2287122347-3831853411-1151728686-1001\Software\AppDataLow\Software\Crossrider
[-] Key deleted: HKU\S-1-5-21-2287122347-3831853411-1151728686-1001\Software\AppDataLow\Software\Freecause
[-] Key deleted: HKU\S-1-5-21-2287122347-3831853411-1151728686-1001\Software\AppDataLow\Software\Yahoo\Companion
[-] Key deleted: HKCU\Software\Microsoft\Internet Explorer\InternetRegistry\REGISTRY\USER\S-1-5-21-2287122347-3831853411-1151728686-1001\Software\BEFRUGAL
[#] Key deleted on reboot: HKCU\Software\BEFRUGAL
[#] Key deleted on reboot: HKCU\Software\Reimage
[#] Key deleted on reboot: HKCU\Software\SlimWare Utilities Inc
[#] Key deleted on reboot: HKCU\Software\Yahoo\Companion
[#] Key deleted on reboot: HKCU\Software\Yahoo\YFriendsBar
[#] Key deleted on reboot: HKCU\Software\YahooPartnerToolbar
[#] Key deleted on reboot: HKCU\Software\Local AppWizard-Generated Applications\Reimage - Windows Problem Relief.
[#] Key deleted on reboot: HKCU\Software\AppDataLow\Software\ConduitSearchScopes
[#] Key deleted on reboot: HKCU\Software\AppDataLow\Software\Crossrider
[#] Key deleted on reboot: HKCU\Software\AppDataLow\Software\Freecause
[#] Key deleted on reboot: HKCU\Software\AppDataLow\Software\Yahoo\Companion
[-] Key deleted: HKLM\SOFTWARE\Conduit
[-] Key deleted: HKLM\SOFTWARE\Freeze.com
[-] Key deleted: HKLM\SOFTWARE\SlimWare Utilities Inc
[-] Key deleted: HKLM\SOFTWARE\Trymedia Systems
[-] Key deleted: HKLM\SOFTWARE\W3I
[-] Key deleted: HKLM\SOFTWARE\Yahoo\Companion
[-] Key deleted: HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{EE171732-BEB4-4576-887D-CB62727F01CA}
[#] Key deleted on reboot: [x64] HKCU\Software\Microsoft\Internet Explorer\InternetRegistry\REGISTRY\USER\S-1-5-21-2287122347-3831853411-1151728686-1001\Software\BEFRUGAL
[#] Key deleted on reboot: [x64] HKCU\Software\BEFRUGAL
[#] Key deleted on reboot: [x64] HKCU\Software\Reimage
[#] Key deleted on reboot: [x64] HKCU\Software\SlimWare Utilities Inc
[#] Key deleted on reboot: [x64] HKCU\Software\Yahoo\Companion
[#] Key deleted on reboot: [x64] HKCU\Software\Yahoo\YFriendsBar
[#] Key deleted on reboot: [x64] HKCU\Software\YahooPartnerToolbar
[#] Key deleted on reboot: [x64] HKCU\Software\Local AppWizard-Generated Applications\Reimage - Windows Problem Relief.
[#] Key deleted on reboot: [x64] HKCU\Software\AppDataLow\Software\ConduitSearchScopes
[#] Key deleted on reboot: [x64] HKCU\Software\AppDataLow\Software\Crossrider
[#] Key deleted on reboot: [x64] HKCU\Software\AppDataLow\Software\Freecause
[#] Key deleted on reboot: [x64] HKCU\Software\AppDataLow\Software\Yahoo\Companion
[-] Key deleted: [x64] HKLM\SOFTWARE\Reimage
[-] Key deleted: [x64] HKLM\SOFTWARE\Microsoft\Internet Explorer\SearchScopes\{AFBCB7E0-F91A-4951-9F31-58FEE57A25C4}
[-] Key deleted: HKCU\Software\Microsoft\Internet Explorer\DOMStorage\azlyrics.com
[#] Key deleted on reboot: [x64] HKCU\Software\Microsoft\Internet Explorer\DOMStorage\azlyrics.com
[-] Key deleted: HKLM\SOFTWARE\Classes\AppID\REI_AxControl.DLL
[-] Key deleted: HKLM\SOFTWARE\Classes\AppID\YMERemote.DLL
[-] Value deleted: HKLM\SOFTWARE\Microsoft\Internet Explorer\New Windows\Allow [*.crossrider.com]
***** [ Web browsers ] *****
*************************
:: "Tracing" keys deleted
:: Winsock settings cleared
*************************
C:\AdwCleaner\AdwCleaner[C0].txt - [9342 Bytes] - [29/10/2016 10:37:04]
C:\AdwCleaner\AdwCleaner[S0].txt - [8943 Bytes] - [29/10/2016 10:32:33]
########## EOF - C:\AdwCleaner\AdwCleaner[C0].txt - [9488 Bytes] ##########
Malwarebytes Anti-Malware
www.malwarebytes.org
Scan Date: 10/29/2016
Scan Time: 11:00 AM
Logfile: malwarebytes scan 10-29-2016.txt
Administrator: Yes
Version: 2.2.1.1043
Malware Database: v2016.10.29.05
Rootkit Database: v2016.09.26.02
License: Trial
Malware Protection: Enabled
Malicious Website Protection: Enabled
Self-protection: Disabled
OS: Windows 7 Service Pack 1
CPU: x64
File System: NTFS
User: Sasha22
Scan Type: Threat Scan
Result: Completed
Objects Scanned: 388222
Time Elapsed: 14 min, 1 sec
Memory: Enabled
Startup: Enabled
Filesystem: Enabled
Archives: Enabled
Rootkits: Disabled
Heuristics: Enabled
PUP: Enabled
PUM: Enabled
Processes: 0
(No malicious items detected)
Modules: 0
(No malicious items detected)
Registry Keys: 5
PUP.Optional.MyScrapNook, HKU\S-1-5-21-2287122347-3831853411-1151728686-1001\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXT\STATS\{0A4D512D-697E-4AD5-872D-5A9941AF6EBB}, Quarantined, [7c7d0b93504afa3c6993068bd72be61a],
Adware.GamePlayLabs, HKLM\SOFTWARE\WOW6432NODE\MICROSOFT\INTERNET EXPLORER\LOW RIGHTS\ELEVATIONPOLICY\{65bcd620-07dd-012f-819f-073cf1b8f7c6}, Quarantined, [b148732bdbbf2511cd1a950209f9f907],
PUP.Optional.MyScrapNook, HKLM\SOFTWARE\CLASSES\INTERFACE\{82024F98-F9FB-47F4-860F-887E41883C9D}, Quarantined, [82773a644f4bb18545bc69290101a858],
PUP.Optional.MyScrapNook, HKLM\SOFTWARE\CLASSES\TypeLib\{C260ADF2-154F-4227-9C73-651E25F22CBB}, Quarantined, [c3367925d9c1ce6852afafe3b54d09f7],
PUP.Optional.Telstra.ChrPRST, HKLM\SOFTWARE\WOW6432NODE\GOOGLE\CHROME\EXTENSIONS\edmgmpmklgfbohogafcfobonnkogchec, Quarantined, [20d927774c4e0f27af7dc61b2bd8e020],
Registry Values: 0
(No malicious items detected)
Registry Data: 0
(No malicious items detected)
Folders: 5
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_0, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_0\CVS, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_1, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_1\CVS, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
Files: 41
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00003460.tmp, Quarantined, [ad4cb7e78218f046a8d5324fd72a15eb],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00003467.tmp, Quarantined, [5b9e732b7426d95d82fb51309869ba46],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00008870.tmp, Quarantined, [b544930b3c5e62d44f2e6120a65bb44c],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00010823.tmp, Quarantined, [6f8a89158f0bdb5b86f70e7317ea9f61],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00014461.tmp, Quarantined, [7683801e7b1fff37730a1d647f82758b],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00016130.tmp, Quarantined, [da1fb2ecd3c7c96d5d20532e19e855ab],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00018047.tmp, Quarantined, [6f8ae2bc6e2c6bcbaad3cdb4c83943bd],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00018683.tmp, Quarantined, [7188dac4a9f11c1a49347b06f20f4ab6],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00020233.tmp, Quarantined, [e712722cf2a89b9b0f6e6b161de4af51],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00020331.tmp, Quarantined, [b9400d915a4022149ce19ce5eb166799],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00022387.tmp, Quarantined, [8871b8e6722805316a136a178e73eb15],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00024186.tmp, Quarantined, [807987179505f541e895621f4cb59967],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00026358.tmp, Quarantined, [1edb613df3a751e5324b720fa45d10f0],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00027024.tmp, Quarantined, [42b7e1bd5a401d19b9c4b2cf1ee34ab6],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00029836.tmp, Quarantined, [8673c3dba4f6d264b2cb58293dc4aa56],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00030085.tmp, Quarantined, [8277128c5d3d74c21e5fceb33cc5629e],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00031393.tmp, Quarantined, [9069742abae07cba76078100f908ea16],
Trojan.Agent.ENM, C:\Program Files (x86)\Internet Explorer\00031478.tmp, Quarantined, [6495a3fb59410b2b700db7ca7d8429d7],
Adware.TryMedia, C:\Users\Public\Downloads\BigCityAdventureSF_EN-dm.exe, Quarantined, [6297623ca0faee48bc728652fb06b050],
Adware.TryMedia, C:\Users\Public\Downloads\DeepVoyage-dm.exe, Quarantined, [11e807973664c670dd51894f9f626e92],
Adware.TryMedia, C:\Users\Public\Downloads\SolitaireChallenge-dm.exe, Quarantined, [d326237b039771c51b133c9cd031b947],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_0\manifest.json, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_0\motiverequest.html, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_0\CVS\Entries, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_0\CVS\Entries.Extra, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_0\CVS\Entries.Extra.Old, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_0\CVS\Entries.Old, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_0\CVS\Repository, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_0\CVS\Root, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_0\CVS\Tag, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_0\CVS\Template, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_1\manifest.json, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_1\motiverequest.html, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_1\CVS\Entries, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_1\CVS\Entries.Extra, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_1\CVS\Entries.Extra.Old, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_1\CVS\Entries.Old, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_1\CVS\Repository, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_1\CVS\Root, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_1\CVS\Tag, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
PUP.Optional.Telstra.ChrPRST, C:\Users\Sasha22\AppData\Local\Google\Chrome\User Data\Default\Extensions\edmgmpmklgfbohogafcfobonnkogchec\1.0_1\CVS\Template, Quarantined, [9d5c2d712476e4523b95c004a75b6898],
Physical Sectors: 0
(No malicious items detected)
(end)
Hope this is it. Thanks for all your help. Sasha22
|
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Oct 29, 2016 18:40:06 GMT -8
Do not remove the work files yet; we may need them later on. Besides, I like to use a cleanup tool that removes the malware fighting tools, logs and any system setting changes that were made. I will direct you in running that tool soon. Go to Emsisoft and download the Emsisoft Free Emergency Kit from here. - Double click on the EmsisoftEmergencyKit.exe file and then click on Extract to unpack the files (the default directory of C:\EEK is fine).
- Go to the new directory and right click on Start Emergency Kit Scanner.exe and choose 'Run as Administrator'.
- Once the scanner loads, allow it check for updates.
- When the updates are finished, click the BACK button to return to the main menu.
- Click on the SCAN and select Malware Scan to start scanning your system. Please enable the PUP detection option, if it asks.
- If the scan finds anything, it will open a scan finding window. Please click on View Report; copy this report and paste it here in reply post.
- Please close the Emergency Kit Scanner program now.
|
|
