|
|
Post by cnardone on Oct 12, 2016 19:46:31 GMT -8
|
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Oct 12, 2016 20:55:54 GMT -8
FIRST >>>>Please go to START (Windows Orb) >> Control Panel >> Uninstall a Program or Programs and Features and remove the following (if listed): QuickTime 7To do so, left clicking on the name once and then click Uninstall/Change at the bar above the list window. Follow the prompts of the uninstaller BUT please read carefully any questions it asks before answering; some uninstallers will try and deceive you into keeping the software. SECOND >>>>Open notepad by pressing the Windows Key + R key, typing notepad in the Run box and pressing Enter. Please copy the contents of the quote box below. To do this highlight the contents of the box and right click on it and select copy. Paste this into the open notepad. Save it to your desktop as fixlist.txtNOTE. It's important that both files, FRST64 and fixlist.txt are in the same location or the fix will not work. NOTICE: This script was written specifically for this user, for use on that particular machine. Running this on another machine may cause damage to your operating systemStart FRST that is on the desktop by right clicking on file and selecting "Run as Administrator..." and press the Fix button just once and wait.  If for some reason the tool needs a restart, please make sure you let the system restart normally. After that let the tool complete its run. When finished FRST will generate a log on the Desktop (Fixlog.txt). Please post it to your reply. LAST >>>>How is your system running now? Does Norton still find Trojan.Kotverlnk ? If so does it tell you were the file is located?
|
|
|
|
Post by cnardone on Oct 12, 2016 22:51:20 GMT -8
I ran a full system scan on Norton. The virus is still there. This is the file it is listed under: C:\users\ChrisNPC\AppData\Local\f37fd\288f6.Ink wikisend.com/download/572354/Fixlog.txtThank you for your continued assistance on this. |
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Oct 13, 2016 0:03:01 GMT -8
We need to get a fresh set of logs but there needs to be some changes done before running the scanner. First of all, disable or turn off SpyBot Search and Destroy. Instructions on how to do this can be found here. Second, both users profiles need to be loaded before the scan is run. To do this, login to one of the users (ChrisNPC or SandyPC) and then go to Start > Switch User and login as the other user. This allows the FRST scanner to see all the data from each user. Read Slowly and all of it.If you still have a Addition.txt log file on your desktop, please delete it now. Start FRST64 that is on your Desktop by double clicking and allowing the software to run when the User Access Control asks (if it does). The tool will start to run. When the tool opens click Yes to disclaimer. (if it does) Select Additional.txt in the Optional Scans section of FRST64. Also, select the 90 Days Files. Press Scan button. It will make two logs ( FRST.txt and addition.txt) on your Desktop. Please attach the logs in your reply back. Or open the logs in notepad and copy the logs and paste back in a message as a reply. ( Ask if you don't know how to do either of these). Notes:
If your Security software blocks the running or download of FRST / FRST64, please disable the security software or make an exception for this file. FRST is updated very frequently and is safe to run but because of the frequent changes (to keep up with newest malware techniques) most Security Software does not approve of the unknown file. Right now the forum will not allow one to attach the Addition.txt file so please use wikisend.com or pastebin.com to upload the file and then post the download link here in your reply post. |
|
|
|
Post by cnardone on Oct 13, 2016 20:20:16 GMT -8
With regards to the SpyBot Live Protection. When I click on the icon near the clock of my computer, it says Live Protection is already off. But, it does say Internet Protection: Full. I have the free version, and do not see anything in the Start Center that says "Live Protection". The window that did come up states, "Live Protection requires a valid license to run. This component is only available in the following editions: Home, Professional, Corporate & Technician Edition." Unless there is something else that should be done, I am going to post my log files. wikisend.com/download/316310/Addition.txtwikisend.com/download/342708/FRST.txt |
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Oct 13, 2016 22:02:04 GMT -8
FIRST >>>>Open notepad by pressing the Windows Key + R key, typing notepad in the Run box and pressing Enter. Please copy the contents of the quote box below. To do this highlight the contents of the box and right click on it and select copy. Paste this into the open notepad. Save it to your desktop as fixlist.txtNOTE. It's important that both files, FRST64 and fixlist.txt are in the same location or the fix will not work. NOTICE: This script was written specifically for this user, for use on that particular machine. Running this on another machine may cause damage to your operating systemStart FRST that is on the desktop by right clicking on file and selecting "Run as Administrator..." and press the Fix button just once and wait.  If for some reason the tool needs a restart, please make sure you let the system restart normally. After that let the tool complete its run. When finished FRST will generate a log on the Desktop (Fixlog.txt). Please post it to your reply. SECOND >>>>Search with FRST [/b] button. It will produce a log called RegSearch.txt in the same directory the tool is run from. Please copy and paste log back here. [/ul] LAST >>>>I need both logs: The Fixlog.txt log file and the RegSearch.txt log file. You shoul be able to attach the file to a post; there should be no need for wikisend.com for these files.
|
|
|
|
Post by cnardone on Oct 13, 2016 23:01:51 GMT -8
Below is the fixlog text...
Fix result of Farbar Recovery Scan Tool (x64) Version: 13-10-2016
Ran by ChrisNPC (13-10-2016 23:46:18) Run:2
Running from C:\Users\ChrisNPC\Desktop
Loaded Profiles: SandyPC & ChrisNPC (Available Profiles: SandyPC & ChrisNPC)
Boot Mode: Normal
==============================================
fixlist content:
*****************
Start
CreateRestorePoint:
CloseProcesses:
2016-07-17 23:28 - 2016-07-25 11:10 - 00000000 ____D C:\Users\ChrisNPC\AppData\Roaming\8e4d4
2016-07-17 23:28 - 2016-07-25 11:10 - 00000000 ____D C:\Users\ChrisNPC\AppData\Local\f37fd
Shortcut: C:\Users\ChrisNPC\AppData\Local\f37fd\288f6.lnk -> C:\Users\ChrisNPC\AppData\Local\f37fd\afa7a.bat (No File)
cmd: ipconfig /flushdns
cmd: netsh advfirewall reset
cmd: netsh advfirewall set allprofiles state on
Reg: reg delete HKLM\SOFTWARE\Policies\Microsoft\Windows\IPSec\Policy\Local /f
Reg: reg add HKLM\SOFTWARE\Policies\Microsoft\Windows\IPSec\Policy\Local /f
CMD: bitsadmin /reset /allusers
RemoveProxy:
EmptyTemp:
Reboot:
end
*****************
Restore point was successfully created.
Processes closed successfully.
C:\Users\ChrisNPC\AppData\Roaming\8e4d4 => moved successfully
C:\Users\ChrisNPC\AppData\Local\f37fd => moved successfully
C:\Users\ChrisNPC\AppData\Local\f37fd\288f6.lnk => not found.
========= ipconfig /flushdns =========
Windows IP Configuration
Successfully flushed the DNS Resolver Cache.
========= End of CMD: =========
========= netsh advfirewall reset =========
Ok.
========= End of CMD: =========
========= netsh advfirewall set allprofiles state on =========
Ok.
========= End of CMD: =========
========= reg delete HKLM\SOFTWARE\Policies\Microsoft\Windows\IPSec\Policy\Local /f =========
The operation completed successfully.
========= End of Reg: =========
========= reg add HKLM\SOFTWARE\Policies\Microsoft\Windows\IPSec\Policy\Local /f =========
The operation completed successfully.
========= End of Reg: =========
========= bitsadmin /reset /allusers =========
BITSADMIN version 3.0
BITS administration utility.
(C) Copyright 2000-2006 Microsoft Corp.
BITSAdmin is deprecated and is not guaranteed to be available in future versions of Windows.
Administrative tools for the BITS service are now provided by BITS PowerShell cmdlets.
0 out of 0 jobs canceled.
========= End of CMD: =========
========= RemoveProxy: =========
HKU\.DEFAULT\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Connections\\DefaultConnectionSettings => value removed successfully
HKU\.DEFAULT\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Connections\\SavedLegacySettings => value removed successfully
HKU\S-1-5-21-610429884-3309474231-1676844322-1002\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Connections\\DefaultConnectionSettings => value removed successfully
HKU\S-1-5-21-610429884-3309474231-1676844322-1002\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Connections\\SavedLegacySettings => value removed successfully
HKU\S-1-5-21-610429884-3309474231-1676844322-1003\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Connections\\DefaultConnectionSettings => value removed successfully
HKU\S-1-5-21-610429884-3309474231-1676844322-1003\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Connections\\SavedLegacySettings => value removed successfully
========= End of RemoveProxy: =========
=========== EmptyTemp: ==========
BITS transfer queue => 2222231 B
DOMStore, IE Recovery, AppCache, Feeds Cache, Thumbcache, IconCache => 15161133 B
Java, Flash, Steam htmlcache => 13381067 B
Windows/system/drivers => 56895 B
Edge => 212918529 B
Chrome => 0 B
Firefox => 0 B
Opera => 0 B
Temp, IE cache, history, cookies, recent:
Default => 0 B
ProgramData => 0 B
Public => 0 B
systemprofile => 0 B
systemprofile32 => 0 B
LocalService => 20516192 B
NetworkService => 0 B
SandyPC => 10221346 B
ChrisNPC => 23217984 B
RecycleBin => 47605 B
EmptyTemp: => 283.9 MB temporary data Removed.
================================
The system needed a reboot.
==== End of Fixlog 23:47:25 ====
Below is the SearchReg text...
Farbar Recovery Scan Tool (x64) Version: 13-10-2016
Ran by ChrisNPC (13-10-2016 23:59:02)
Running from C:\Users\ChrisNPC\Desktop
Boot Mode: Normal
================== Search Registry: "C:\Windows\system32\mshta.exe" ===========
====== End of Search ======
|
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Oct 13, 2016 23:17:58 GMT -8
Is Norton still finding the Trojan?
|
|
|
|
Post by cnardone on Oct 14, 2016 17:35:15 GMT -8
I just ran the Norton anti-virus and it came back clean. Thank you very much for your help on this. I appreciate it!
What's left to do?
Thx.
|
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Oct 14, 2016 19:29:45 GMT -8
FIRST >>>>Junkware Removal ToolPlease download JRT from here to your desktop. Note: Temporarily disable/shut down your protection software now to avoid potential conflicts, how to do so can be read here.Double click the JRT.exe file to run the application. The application will open an Command Prompt window and run from there (this is normal for this program, so not to be alarmed). When it is asked, press any key to allow the program to continue / run. This will create a log on the desktop; please copy and paste the JRT.txt log text in your next post. Note: After the log file is created, please enable your protection software / reboot your system and verify your protection software is enabled.SECOND >>>>AdwCleaner by XplodeDownload AdwCleaner from here or from here. Save the file to the desktop. NOTE: If you are using IE 8 or above you may get a warning that stops the program from downloading. Just click on the warning and allow the download to complete. Close all open windows and browsers.Vista/7/8 users: Right click the AdwCleaner icon on the desktop, click Run as administrator and accept the UAC prompt to run AdwCleaner. You will see the following console:  Click the Scan button and wait for the scan to finish. After the Scan has finished the window may or may not show what it found and above, in the progress bar, you will see: Waiting for action. Please uncheck elements you don't want to remove.Click the Clean button. Everything checked will be deleted. When the program has finished cleaning a report appears. Once done it will ask to reboot, allow this 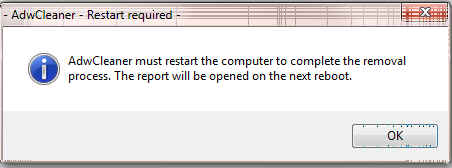 On reboot a log will be produced please copy / paste that in your next reply. This report is also saved to C:\AdwCleaner\AdwCleaner[C#].txtOptional: NOTE: If you see AVG Secure Search being targeted for deletion, Here's Why and Here. You can always Reinstall it.
|
|