dk23
New Helpee

Posts: 7 
|
Post by dk23 on Feb 7, 2017 15:06:37 GMT -8
|
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Feb 13, 2017 0:02:33 GMT -8
We will try our best to help you. For now it would be best to know which Ransomware exactly we are dealing with. Please go to this web site ( ID Ransomware ) and upload the ransom note file and / or an encrypted file. The web service there will examine both and determine exactly what version of Ramsomware we are dealing with. DO NOT DO ANYTHING ELSE FOR NOW AS I DO SEE SOME OTHER MALWARE BUT DO NOT WANT TO BLINDLY GO HACKING ABOUT IN YOUR SYSTEM!!! Let me know the results from the examination site.
You may also want to visit this site ( www.nomoreransom.org/ ) for more information and help. |
|
dk23
New Helpee

Posts: 7 
|
Post by dk23 on Feb 13, 2017 1:51:17 GMT -8
Thanks so much for your help.
Here is the result;
Crypt0L0cker
This ransomware may be decryptable under certain circumstances.
Please refer to the appropriate guide for more information.
Identified by
ransomnote_filename: HOW_TO_RESTORE_FILES.txt
ransomnote_keyword: "Crypt0L0cker"
|
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Feb 13, 2017 15:48:01 GMT -8
So it is confirmed that this is Crypt0L0cker. I hope you read the instructions / information and looked into trying to decrypting your files. I need to ask a few questions before we continue: Do you have a backup copy of your files? You understand that I can remove the malware that encrypted your files BUT that does not get your files back?
The following will remove the active malware; only do this when you have a backup and understand what I asked you above: Open notepad by pressing the Windows Key + R key, typing notepad in the Run box and pressing Enter. Please copy the contents of the quote box below. To do this highlight the contents of the box and right click on it and select copy. Paste this into the open notepad. Save it to your desktop as fixlist.txtNOTE. It's important that both files, FRST64 and fixlist.txt are in the same location or the fix will not work. NOTICE: This script was written specifically for this user, for use on that particular machine. Running this on another machine may cause damage to your operating systemStart FRST that is on the desktop by right clicking on file and selecting "Run as Administrator..." and press the Fix button just once and wait.  If for some reason the tool needs a restart, please make sure you let the system restart normally. After that let the tool complete its run. When finished FRST will generate a log on the Desktop (Fixlog.txt). Please post it to your reply. |
|
dk23
New Helpee

Posts: 7 
|
Post by dk23 on Feb 17, 2017 19:45:18 GMT -8
Fix result of Farbar Recovery Scan Tool (x64) Version: 18-02-2017
Ran by Kelly's (18-02-2017 13:45:08) Run:1
Running from C:\Users\Kelly's\Desktop
Loaded Profiles: Kelly's (Available Profiles: Kelly's & DefaultAppPool)
Boot Mode: Normal
==============================================
fixlist content:
*****************
Start
CreateRestorePoint:
CloseProcesses:
HKU\S-1-5-21-2498485014-2158400492-1884474410-1001\...\Run: [iqafykyr] => C:\ProgramData\ewedives.exe [440007 2017-02-08] ()
C:\ProgramData\ewedives.exe
HKU\S-1-5-21-2498485014-2158400492-1884474410-1001\...\RunOnce: [Uninstall C:\Users\Kelly's\AppData\Local\Microsoft\OneDrive\17.3.6390.0509\amd64] => C:\WINDOWS\system32\cmd.exe /q /c rmdir /s /q "C:\Users\Kelly's\AppData\Local\Microsoft\OneDrive\17.3.6390.0509\amd64"
BHO: No Name -> {B4F3A835-0E21-4959-BA22-42B3008E02FF} -> No File
Toolbar: HKU\S-1-5-21-2498485014-2158400492-1884474410-1001 -> No Name - {4BAAC1B8-0800-42C9-8FA6-08B211F356B8} - No File
CHR Extension: (Google Slides) - C:\Users\Kelly's\AppData\Local\Google\Chrome\User Data\Default\Extensions\aapocclcgogkmnckokdopfmhonfmgoek [2015-07-07]
CHR Extension: (Google Drive) - C:\Users\Kelly's\AppData\Local\Google\Chrome\User Data\Default\Extensions\apdfllckaahabafndbhieahigkjlhalf [2015-12-15]
CHR Extension: (Google Search) - C:\Users\Kelly's\AppData\Local\Google\Chrome\User Data\Default\Extensions\coobgpohoikkiipiblmjeljniedjpjpf [2015-12-15]
CHR Extension: (Chrome Web Store Payments) - C:\Users\Kelly's\AppData\Local\Google\Chrome\User Data\Default\Extensions\nmmhkkegccagdldgiimedpiccmgmieda [2016-04-12]
CHR Extension: (Chrome Media Router) - C:\Users\Kelly's\AppData\Local\Google\Chrome\User Data\Default\Extensions\pkedcjkdefgpdelpbcmbmeomcjbeemfm [2016-12-17]
U3 idsvc; no ImagePath
2017-02-08 06:58 - 2017-02-08 09:18 - 00003602 _____ C:\Users\Kelly's\Desktop\HOW_TO_RESTORE_FILES.html
2017-02-08 06:58 - 2017-02-08 09:18 - 00001112 _____ C:\Users\Kelly's\Desktop\HOW_TO_RESTORE_FILES.txt
2017-02-08 06:58 - 2017-02-08 06:58 - 00440007 _____ C:\ProgramData\ewedives.exe
2017-02-08 06:58 - 2017-02-08 06:58 - 00003602 _____ C:\Users\Kelly's\Downloads\HOW_TO_RESTORE_FILES.html
2017-02-08 06:58 - 2017-02-08 06:58 - 00003602 _____ C:\Users\Kelly's\Documents\HOW_TO_RESTORE_FILES.html
2017-02-08 06:58 - 2017-02-08 06:58 - 00003602 _____ C:\Users\Kelly's\AppData\LocalLow\HOW_TO_RESTORE_FILES.html
2017-02-08 06:58 - 2017-02-08 06:58 - 00001112 _____ C:\Users\Kelly's\Downloads\HOW_TO_RESTORE_FILES.txt
2017-02-08 06:58 - 2017-02-08 06:58 - 00001112 _____ C:\Users\Kelly's\Documents\HOW_TO_RESTORE_FILES.txt
2017-02-08 06:58 - 2017-02-08 06:58 - 00001112 _____ C:\Users\Kelly's\AppData\LocalLow\HOW_TO_RESTORE_FILES.txt
2017-02-08 06:57 - 2017-02-08 06:59 - 00000000 ____D C:\ProgramData\uwupefovygigylih
2017-02-08 08:53 - 2017-02-08 08:53 - 0164531 _____ () C:\ProgramData\ejofarym.png
2017-02-08 06:58 - 2017-02-08 06:58 - 0440007 _____ () C:\ProgramData\ewedives.exe
2017-02-08 07:24 - 2017-02-08 07:24 - 0164531 _____ () C:\ProgramData\olhlahoc.png
2017-02-08 09:18 - 2017-02-08 09:18 - 0164531 _____ () C:\ProgramData\ymebymyh.png
C:\ProgramData\ewedives.exe
2017-02-07 09:52 - 2017-02-07 09:52 - 0061440 _____ () C:\Users\Kelly's\AppData\Local\Temp\commensalism.dll
2017-01-13 10:19 - 2017-01-13 10:19 - 0737856 _____ (Oracle Corporation) C:\Users\Kelly's\AppData\Local\Temp\jre-8u111-windows-au.exe
2017-02-08 06:57 - 2017-02-08 06:58 - 0440007 _____ () C:\Users\Kelly's\AppData\Local\Temp\lleco.exe
Task: {035CCE54-A5DB-4984-9202-55B13343359C} - \Microsoft\Windows\Setup\GWXTriggers\Telemetry-4xd -> No File <==== ATTENTION
Task: {09704B21-568E-4D81-8A8D-466D3BB3D156} - \Microsoft\Windows\Setup\GWXTriggers\Time-5d -> No File <==== ATTENTION
Task: {1B59F4B0-C373-4F85-9D2D-F8D7DB57C490} - \OfficeSoftwareProtectionPlatform\SvcRestartTask -> No File <==== ATTENTION
Task: {243E2D2E-80CA-4CC1-814C-F30977F7DBEF} - \Microsoft\Windows\Setup\GWXTriggers\Logon-5d -> No File <==== ATTENTION
Task: {2CDADE3F-C5CA-498C-8728-1C96B1F3F64C} - \Microsoft\Windows\Setup\GWXTriggers\OutOfSleep-5d -> No File <==== ATTENTION
Task: {3802942E-6AF0-4E91-ACAB-C2CF70CEE633} - \Microsoft\Windows\Setup\GWXTriggers\MachineUnlock-5d -> No File <==== ATTENTION
Task: {38F1ED5B-C0D0-44F6-ACA2-4352B693E5CE} - System32\Tasks\{EFD9583B-E3D8-4781-ADCF-2C5B7EB85C7F} => pcalua.exe -a C:\Users\Kelly's\Downloads\install_flashplayer15x32_mssd_aaa_aih.exe -d C:\Users\Kelly's\Downloads
Task: {3D3E152E-9492-4153-A288-9818EA85C142} - \Microsoft\Windows\Setup\GWXTriggers\refreshgwxconfig-B -> No File <==== ATTENTION
Task: {47F9A754-CA5F-47B4-A5E6-1E975C2E444F} - \Microsoft\Windows\Setup\gwx\refreshgwxconfig -> No File <==== ATTENTION
Task: {4C6710D6-0E4A-4997-8D02-DAE196412740} - \Microsoft\Windows\Setup\gwx\refreshgwxcontent -> No File <==== ATTENTION
Task: {6CB360EB-851E-4D11-84C2-9EE479F1AA8C} - \Microsoft\Windows\Setup\GWXTriggers\OutOfIdle-5d -> No File <==== ATTENTION
Task: {6E0F300F-77C3-420D-8260-DCCEDC39B3F5} - \Microsoft\Windows\Setup\gwx\refreshgwxconfigandcontent -> No File <==== ATTENTION
Task: {7261ABA5-1BB8-49CE-9C66-28B7CBF261E5} - \Microsoft\Windows\Setup\gwx\launchtrayprocess -> No File <==== ATTENTION
cmd: ipconfig /flushdns
cmd: netsh advfirewall reset
cmd: netsh advfirewall set allprofiles state on
Reg: reg delete HKLM\SOFTWARE\Policies\Microsoft\Windows\IPSec\Policy\Local /f
Reg: reg add HKLM\SOFTWARE\Policies\Microsoft\Windows\IPSec\Policy\Local /f
CMD: bitsadmin /reset /allusers
RemoveProxy:
EmptyTemp:
Reboot:
end
*****************
Restore point was successfully created.
Processes closed successfully.
HKU\S-1-5-21-2498485014-2158400492-1884474410-1001\Software\Microsoft\Windows\CurrentVersion\Run\\iqafykyr => value not found.
"C:\ProgramData\ewedives.exe" => not found.
HKU\S-1-5-21-2498485014-2158400492-1884474410-1001\Software\Microsoft\Windows\CurrentVersion\RunOnce\\Uninstall C:\Users\Kelly's\AppData\Local\Microsoft\OneDrive\17.3.6390.0509\amd64 => value removed successfully
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{B4F3A835-0E21-4959-BA22-42B3008E02FF} => key removed successfully
HKCR\CLSID\{B4F3A835-0E21-4959-BA22-42B3008E02FF} => key not found.
HKU\S-1-5-21-2498485014-2158400492-1884474410-1001\Software\Microsoft\Internet Explorer\Toolbar\WebBrowser\\{4BAAC1B8-0800-42C9-8FA6-08B211F356B8} => value removed successfully
HKCR\CLSID\{4BAAC1B8-0800-42C9-8FA6-08B211F356B8} => key not found.
C:\Users\Kelly's\AppData\Local\Google\Chrome\User Data\Default\Extensions\aapocclcgogkmnckokdopfmhonfmgoek => moved successfully
C:\Users\Kelly's\AppData\Local\Google\Chrome\User Data\Default\Extensions\apdfllckaahabafndbhieahigkjlhalf => moved successfully
C:\Users\Kelly's\AppData\Local\Google\Chrome\User Data\Default\Extensions\coobgpohoikkiipiblmjeljniedjpjpf => moved successfully
C:\Users\Kelly's\AppData\Local\Google\Chrome\User Data\Default\Extensions\nmmhkkegccagdldgiimedpiccmgmieda => moved successfully
C:\Users\Kelly's\AppData\Local\Google\Chrome\User Data\Default\Extensions\pkedcjkdefgpdelpbcmbmeomcjbeemfm => moved successfully
HKLM\System\CurrentControlSet\Services\idsvc => key removed successfully
idsvc => service removed successfully
"C:\Users\Kelly's\Desktop\HOW_TO_RESTORE_FILES.html" => not found.
"C:\Users\Kelly's\Desktop\HOW_TO_RESTORE_FILES.txt" => not found.
"C:\ProgramData\ewedives.exe" => not found.
C:\Users\Kelly's\Downloads\HOW_TO_RESTORE_FILES.html => moved successfully
"C:\Users\Kelly's\Documents\HOW_TO_RESTORE_FILES.html" => not found.
C:\Users\Kelly's\AppData\LocalLow\HOW_TO_RESTORE_FILES.html => moved successfully
C:\Users\Kelly's\Downloads\HOW_TO_RESTORE_FILES.txt => moved successfully
"C:\Users\Kelly's\Documents\HOW_TO_RESTORE_FILES.txt" => not found.
C:\Users\Kelly's\AppData\LocalLow\HOW_TO_RESTORE_FILES.txt => moved successfully
C:\ProgramData\uwupefovygigylih => moved successfully
C:\ProgramData\ejofarym.png => moved successfully
"C:\ProgramData\ewedives.exe" => not found.
C:\ProgramData\olhlahoc.png => moved successfully
C:\ProgramData\ymebymyh.png => moved successfully
"C:\ProgramData\ewedives.exe" => not found.
C:\Users\Kelly's\AppData\Local\Temp\commensalism.dll => moved successfully
C:\Users\Kelly's\AppData\Local\Temp\jre-8u111-windows-au.exe => moved successfully
C:\Users\Kelly's\AppData\Local\Temp\lleco.exe => moved successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Plain\{035CCE54-A5DB-4984-9202-55B13343359C} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{035CCE54-A5DB-4984-9202-55B13343359C} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\Microsoft\Windows\Setup\GWXTriggers\Telemetry-4xd => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Plain\{09704B21-568E-4D81-8A8D-466D3BB3D156} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{09704B21-568E-4D81-8A8D-466D3BB3D156} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\Microsoft\Windows\Setup\GWXTriggers\Time-5d => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Plain\{1B59F4B0-C373-4F85-9D2D-F8D7DB57C490} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{1B59F4B0-C373-4F85-9D2D-F8D7DB57C490} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\OfficeSoftwareProtectionPlatform\SvcRestartTask => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Logon\{243E2D2E-80CA-4CC1-814C-F30977F7DBEF} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{243E2D2E-80CA-4CC1-814C-F30977F7DBEF} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\Microsoft\Windows\Setup\GWXTriggers\Logon-5d => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Plain\{2CDADE3F-C5CA-498C-8728-1C96B1F3F64C} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{2CDADE3F-C5CA-498C-8728-1C96B1F3F64C} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\Microsoft\Windows\Setup\GWXTriggers\OutOfSleep-5d => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Plain\{3802942E-6AF0-4E91-ACAB-C2CF70CEE633} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{3802942E-6AF0-4E91-ACAB-C2CF70CEE633} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\Microsoft\Windows\Setup\GWXTriggers\MachineUnlock-5d => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Plain\{38F1ED5B-C0D0-44F6-ACA2-4352B693E5CE} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{38F1ED5B-C0D0-44F6-ACA2-4352B693E5CE} => key removed successfully
C:\WINDOWS\System32\Tasks\{EFD9583B-E3D8-4781-ADCF-2C5B7EB85C7F} => moved successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\{EFD9583B-E3D8-4781-ADCF-2C5B7EB85C7F} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Plain\{3D3E152E-9492-4153-A288-9818EA85C142} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{3D3E152E-9492-4153-A288-9818EA85C142} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\Microsoft\Windows\Setup\GWXTriggers\refreshgwxconfig-B => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Plain\{47F9A754-CA5F-47B4-A5E6-1E975C2E444F} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{47F9A754-CA5F-47B4-A5E6-1E975C2E444F} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\Microsoft\Windows\Setup\gwx\refreshgwxconfig => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Plain\{4C6710D6-0E4A-4997-8D02-DAE196412740} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{4C6710D6-0E4A-4997-8D02-DAE196412740} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\Microsoft\Windows\Setup\gwx\refreshgwxcontent => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Plain\{6CB360EB-851E-4D11-84C2-9EE479F1AA8C} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{6CB360EB-851E-4D11-84C2-9EE479F1AA8C} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\Microsoft\Windows\Setup\GWXTriggers\OutOfIdle-5d => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Plain\{6E0F300F-77C3-420D-8260-DCCEDC39B3F5} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{6E0F300F-77C3-420D-8260-DCCEDC39B3F5} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\Microsoft\Windows\Setup\gwx\refreshgwxconfigandcontent => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Logon\{7261ABA5-1BB8-49CE-9C66-28B7CBF261E5} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{7261ABA5-1BB8-49CE-9C66-28B7CBF261E5} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\Microsoft\Windows\Setup\gwx\launchtrayprocess => key removed successfully
========= ipconfig /flushdns =========
Windows IP Configuration
Successfully flushed the DNS Resolver Cache.
========= End of CMD: =========
========= netsh advfirewall reset =========
Ok.
========= End of CMD: =========
========= netsh advfirewall set allprofiles state on =========
Ok.
========= End of CMD: =========
========= reg delete HKLM\SOFTWARE\Policies\Microsoft\Windows\IPSec\Policy\Local /f =========
The operation completed successfully.
========= End of Reg: =========
========= reg add HKLM\SOFTWARE\Policies\Microsoft\Windows\IPSec\Policy\Local /f =========
The operation completed successfully.
========= End of Reg: =========
========= bitsadmin /reset /allusers =========
BITSADMIN version 3.0
BITS administration utility.
(C) Copyright 2000-2006 Microsoft Corp.
BITSAdmin is deprecated and is not guaranteed to be available in future versions of Windows.
Administrative tools for the BITS service are now provided by BITS PowerShell cmdlets.
Unable to cancel {1F6679D1-73AC-4A1C-9ABA-6F81A2EDAB35}.
{F0D13D3A-BADF-43B0-8A90-DAB0C469F468} canceled.
{0CCAE25E-0999-4BA1-BEE9-F8B68DC40EBA} canceled.
{BAF23602-E3F8-4559-ADC5-EEB41BA2ECCE} canceled.
{CBE955C2-8144-4D76-A398-53A3C5954E9E} canceled.
{1277611F-4C37-42FD-8842-355BCB6BD392} canceled.
5 out of 6 jobs canceled.
========= End of CMD: =========
========= RemoveProxy: =========
HKU\.DEFAULT\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Connections\\DefaultConnectionSettings => value removed successfully
HKU\.DEFAULT\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Connections\\SavedLegacySettings => value removed successfully
HKU\S-1-5-21-2498485014-2158400492-1884474410-1001\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Connections\\DefaultConnectionSettings => value removed successfully
HKU\S-1-5-21-2498485014-2158400492-1884474410-1001\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Connections\\SavedLegacySettings => value removed successfully
========= End of RemoveProxy: =========
=========== EmptyTemp: ==========
BITS transfer queue => 32768 B
DOMStore, IE Recovery, AppCache, Feeds Cache, Thumbcache, IconCache => 183292710 B
Java, Flash, Steam htmlcache => 138557 B
Windows/system/drivers => 185766540 B
Edge => 717891 B
Chrome => 555793655 B
Firefox => 411986750 B
Opera => 0 B
Temp, IE cache, history, cookies, recent:
Default => 80072 B
Users => 0 B
ProgramData => 0 B
Public => 0 B
systemprofile => 0 B
systemprofile32 => 128 B
LocalService => 71194 B
NetworkService => 886462 B
Kelly's => 943969381 B
DefaultAppPool => 33058 B
RecycleBin => 77759 B
EmptyTemp: => 2.1 GB temporary data Removed.
================================
The system needed a reboot.
==== End of Fixlog 13:49:04 ====
|
|
dk23
New Helpee

Posts: 7 
|
Post by dk23 on Feb 17, 2017 19:48:08 GMT -8
Sorry it took a while to find the time.
Thanks
|
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Feb 18, 2017 11:33:39 GMT -8
FIRST >>>>Junkware Removal ToolPlease download JRT from here to your desktop. Note: Temporarily disable/shut down your protection software now to avoid potential conflicts, how to do so can be read here.Double click the JRT.exe file to run the application. The application will open an Command Prompt window and run from there (this is normal for this program, so not to be alarmed). When it is asked, press any key to allow the program to continue / run. This will create a log on the desktop; please copy and paste the JRT.txt log text in your next post. Note: After the log file is created, please enable your protection software / reboot your system and verify your protection software is enabled.SECOND >>>>AdwCleaner by XplodeDownload AdwCleaner from here or from here. Save the file to the desktop. NOTE: If you are using IE 8 or above you may get a warning that stops the program from downloading. Just click on the warning and allow the download to complete. Close all open windows and browsers.Vista/7/8 users: Right click the AdwCleaner icon on the desktop, click Run as administrator and accept the UAC prompt to run AdwCleaner. You will see the following console:  Click the Scan button and wait for the scan to finish. After the Scan has finished the window may or may not show what it found and above, in the progress bar, you will see: Waiting for action. Please uncheck elements you don't want to remove.Click the Clean button. Everything checked will be deleted. When the program has finished cleaning a report appears. Once done it will ask to reboot, allow this 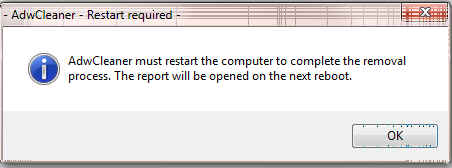 On reboot a log will be produced please copy / paste that in your next reply. This report is also saved to C:\AdwCleaner\AdwCleaner[C#].txtOptional: NOTE: If you see AVG Secure Search being targeted for deletion, Here's Why and Here. You can always Reinstall it.
|
|
dk23
New Helpee

Posts: 7 
|
Post by dk23 on Feb 18, 2017 23:34:54 GMT -8
Junkware Removal Tool (JRT) by Malwarebytes
Version: 8.1.0 (12.05.2016)
Operating System: Windows 10 Pro x64
Ran by Kelly's (Administrator) on 19-Feb-17 at 18:01:06.32
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
File System: 3
Successfully deleted: C:\Users\Kelly's\AppData\Local\{2D3A824A-01B9-4130-BE65-B7A96671B4C5} (Empty Folder)
Successfully deleted: C:\Users\Kelly's\AppData\Local\{2F8B87D7-6603-4A64-8D2D-2928EB73FF46} (Empty Folder)
Successfully deleted: C:\Users\Kelly's\AppData\Local\{3345544B-5380-4555-A3AA-5A78010F3CD7} (Empty Folder)
Registry: 0
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Scan was completed on 19-Feb-17 at 18:02:43.53
End of JRT log
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
|
|
dk23
New Helpee

Posts: 7 
|
Post by dk23 on Feb 18, 2017 23:50:41 GMT -8
# AdwCleaner v6.043 - Logfile created 19/02/2017 at 18:17:20 # Updated on 27/01/2017 by Malwarebytes # Database : 2017-02-13.1 [Server] # Operating System : Windows 10 Pro (X64) # Username : Kelly's - KELLYS-PC # Running from : C:\Users\Kelly's\Desktop\AdwCleaner.exe # Mode: Clean # Support : www.malwarebytes.com/support***** [ Services ] ***** ***** [ Folders ] ***** [#] Folder deleted on reboot: C:\Users\Kelly's\Desktop\PCP ***** [ Files ] ***** ***** [ DLL ] ***** ***** [ WMI ] ***** ***** [ Shortcuts ] ***** ***** [ Scheduled Tasks ] ***** ***** [ Registry ] ***** ***** [ Web browsers ] ***** ************************* :: "Tracing" keys deleted :: Winsock settings cleared ************************* C:\AdwCleaner\AdwCleaner[C0].txt - [808 Bytes] - [19/02/2017 18:17:20] C:\AdwCleaner\AdwCleaner[S0].txt - [1156 Bytes] - [19/02/2017 18:07:59] ########## EOF - C:\AdwCleaner\AdwCleaner[C0].txt - [953 Bytes] ########## |
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Feb 19, 2017 1:12:26 GMT -8
How is your system running now?
|
|