|
|
Post by drbruce on Mar 3, 2017 7:47:31 GMT -8
After many days of Norton Security tell me that this bug was found and quarantined and to restart my computer, only to have the same repeated again and again and again and ...... I finally decided to look into the real way to get rid of it. So, here I am. Please help. Files to follow. Thanks. |
|
|
|
Post by drbruce on Mar 3, 2017 7:54:00 GMT -8
|
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Mar 3, 2017 9:07:35 GMT -8
There are a few other things that could be fixed on the system but let us concentrate on Kotver first. FIRST >>>>Open notepad by pressing the Windows Key + R key, typing notepad in the Run box and pressing Enter. Please copy the contents of the quote box below. To do this highlight the contents of the box and right click on it and select copy. Paste this into the open notepad. Save it to your desktop as fixlist.txtNOTE. It's important that both files, FRST64 and fixlist.txt are in the same location or the fix will not work. NOTICE: This script was written specifically for this user, for use on that particular machine. Running this on another machine may cause damage to your operating systemStart FRST that is on the desktop by right clicking on file and selecting "Run as Administrator..." and press the Fix button just once and wait.  If for some reason the tool needs a restart, please make sure you let the system restart normally. After that let the tool complete its run. When finished FRST will generate a log on the Desktop (Fixlog.txt). Please post it to your reply. SECOND >>>>Please download Malwarebytes Anti-Rootkit from here- Unzip the contents to a folder in a convenient location.
- Open the folder where the contents were unzipped and run mbar.exe
- Follow the instructions in the wizard to update and allow the program to scan your computer for threats.
- Click on the Cleanup button to remove any threats and reboot if prompted to do so.
- Wait while the system shuts down and the cleanup process is performed.
- Perform another scan with Malwarebytes Anti-Rootkit to verify that no threats remain. If they do, then click Cleanup once more and repeat the process.
- When done, please post the two logs produced they will be in the MBAR folder... mbar-log.txt and system-log.txt .
[/ul] LAST >>>>INFO TO REPLY WITH:How is your system running now? The Fixlog.txt text file (you should be able to attach this file; no need for wikisend.com usually). The logs from MBAR - mbar-log.txt and the system-log.txt files please. Any questions? |
|
|
|
Post by drbruce on Mar 3, 2017 13:07:42 GMT -8
Follow up mbar-log was clean.
I assume this resolved the problem. Will let you know in 1-2 days.
Now, what are the other issues that you referred to? |
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Mar 3, 2017 21:39:05 GMT -8
There are some search settings and tasks that need to be cleaned up. The best way to proceed is to have fresh scans from FRST and move on from there. Read Slowly and all of it.If you still have a Addition.txt log file on your desktop, please delete it now. Start FRST64 that is on your Desktop by double clicking and allowing the software to run when the User Access Control asks (if it does). The tool will start to run. When the tool opens click Yes to disclaimer. (if it does) Select Additional.txt and 90 Days Files in the Optional Scans section of FRST64. Press Scan button. It will make two logs ( FRST.txt and addition.txt) on your Desktop. Please post the logs via wikisend.com in your reply back. Notes:
If your Security software blocks the running or download of FRST / FRST64, please disable the security software or make an exception for this file. FRST is updated very frequently and is safe to run but because of the frequent changes (to keep up with newest malware techniques) most Security Software does not approve of the unknown file. Right now the forum will not allow one to attach the Addition.txt file so please use wikisend.com or pastebin.com to upload the file and then post the download link here in your reply post. |
|
|
|
Post by drbruce on Mar 4, 2017 5:01:10 GMT -8
|
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Mar 4, 2017 21:13:53 GMT -8
FIRST >>>>Please go to START (Windows Orb) >> Control Panel >> Uninstall a Program or Programs and Features and remove the following (if listed): Coupon Printer for Windows
PuzzleGamesDaily Internet Explorer Toolbar
SnapMyScreenTo do so, left clicking on the name once and then click Uninstall/Change at the bar above the list window. Follow the prompts of the uninstaller BUT please read carefully any questions it asks before answering; some uninstallers will try and deceive you into keeping the software. SECOND >>>>Open notepad by pressing the Windows Key + R key, typing notepad in the Run box and pressing Enter. Please copy the contents of the quote box below. To do this highlight the contents of the box and right click on it and select copy. Paste this into the open notepad. Save it to your desktop as fixlist.txtNOTE. It's important that both files, FRST64 and fixlist.txt are in the same location or the fix will not work. NOTICE: This script was written specifically for this user, for use on that particular machine. Running this on another machine may cause damage to your operating systemStart FRST that is on the desktop by right clicking on file and selecting "Run as Administrator..." and press the Fix button just once and wait.  If for some reason the tool needs a restart, please make sure you let the system restart normally. After that let the tool complete its run. When finished FRST will generate a log on the Desktop (Fixlog.txt). Please post it to your reply. LAST >>>>INFO TO REPLY WITH:How is your system running now? How did the uninstall(s) go? Any problems? The Fixlog.txt text file (you should be able to attach this file; no need for wikisend.com usually). Any questions?
|
|
|
|
Post by drbruce on Mar 5, 2017 11:55:23 GMT -8
After running FRST64 and starting IE, I had message saying "unknown program wants to change default search engine to "Google" I said NO. Google was and now still is default search engine.
TrojanKotver!gm2 no longer appearing multiple times daily. THANKS
I was getting very often "(multiple website) is not responding" errors, causing IE to attempt (sometime successful, sometime not) to reload page. Any idea to solving this?
Let me know if anything is next in line for fixing.
Thanks Attachments:Fixlog.txt (51.54 KB)
|
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Mar 5, 2017 22:25:01 GMT -8
Just so you are informed, your logs show that Google Chrome is your default browser (that is a system default not nessasarily the browser you use all the time or the most) and your default search engine on ALL browsers was (is?) mysearchdial (MindSpring) not Google. Let's check things out a little further and then see if all is well. FIRST >>>>Junkware Removal ToolPlease download JRT from here to your desktop. Note: Temporarily disable/shut down your protection software now to avoid potential conflicts, how to do so can be read here.Double click the JRT.exe file to run the application. The application will open an Command Prompt window and run from there (this is normal for this program, so not to be alarmed). When it is asked, press any key to allow the program to continue / run. This will create a log on the desktop; please copy and paste the JRT.txt log text in your next post. Note: After the log file is created, please enable your protection software / reboot your system and verify your protection software is enabled.SECOND >>>>AdwCleaner by XplodeDownload AdwCleaner from here or from here. Save the file to the desktop. NOTE: If you are using IE 8 or above you may get a warning that stops the program from downloading. Just click on the warning and allow the download to complete. Close all open windows and browsers.Vista/7/8 users: Right click the AdwCleaner icon on the desktop, click Run as administrator and accept the UAC prompt to run AdwCleaner. You will see the following console:  Click the Scan button and wait for the scan to finish. After the Scan has finished the window may or may not show what it found and above, in the progress bar, you will see: Waiting for action. Please uncheck elements you don't want to remove.Click the Clean button. Everything checked will be deleted. When the program has finished cleaning a report appears. Once done it will ask to reboot, allow this 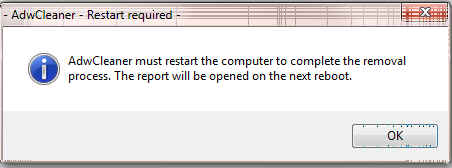 On reboot a log will be produced please copy / paste that in your next reply. This report is also saved to C:\AdwCleaner\AdwCleaner[C#].txtOptional: NOTE: If you see AVG Secure Search being targeted for deletion, Here's Why and Here. You can always Reinstall it. |
|
|
|
Post by drbruce on Mar 7, 2017 7:06:17 GMT -8
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Junkware Removal Tool (JRT) by Malwarebytes
Version: 8.1.1 (02.11.2017)
Operating System: Windows 10 Home x64
Ran by drbruce (Administrator) on Tue 03/07/2017 at 9:35:02.08
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
File System: 5
Successfully deleted: C:\Users\drbruce\AppData\Local\Google\Chrome\User Data\Default\Local Extension Settings\iagcajndpnfncplednpbnkahadegklfa (Folder)
Successfully deleted: C:\Users\drbruce\AppData\Local\mindspark (Folder)
Successfully deleted: C:\Users\drbruce\AppData\Local\pdfforge (Folder)
Successfully deleted: C:\Users\drbruce\AppData\Roaming\opencandy (Folder)
Successfully deleted: C:\Users\drbruce\Documents\my pagemanager (Folder)
Registry: 4
Successfully deleted: HKCU\Software\Google\Chrome\Extensions\iagcajndpnfncplednpbnkahadegklfa (Registry Key)
Successfully deleted: HKCU\Software\Microsoft\Internet Explorer\SearchScopes\{AFBCB7E0-F91A-4951-9F31-58FEE57A25C4} (Registry Key)
Successfully deleted: HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{3A2D5EBA-F86D-4BD3-A177-019765996711} (Registry Key)
Successfully deleted: HKLM\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{3A2D5EBA-F86D-4BD3-A177-019765996711} (Registry Key)
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Scan was completed on Tue 03/07/2017 at 9:37:22.03
End of JRT log
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
# AdwCleaner v6.044 - Logfile created 07/03/2017 at 09:55:26
# Updated on 28/02/2017 by Malwarebytes
# Database : 2017-03-07.1 [Server]
# Operating System : Windows 10 Home (X64)
# Username : drbruce - OFFICE
# Running from : C:\Users\drbruce\Desktop\adwcleaner_6.044.exe
# Mode: Clean
# Support : www.malwarebytes.com/support
***** [ Services ] *****
***** [ Folders ] *****
***** [ Files ] *****
***** [ DLL ] *****
***** [ WMI ] *****
***** [ Shortcuts ] *****
***** [ Scheduled Tasks ] *****
***** [ Registry ] *****
[-] Key deleted: HKLM\SOFTWARE\Google\Chrome\NativeMessagingHosts\com.mindspark.snapmyscreen_bf
[-] Key deleted: HKLM\SOFTWARE\Classes\protector_dll.Protector
[-] Key deleted: HKLM\SOFTWARE\Classes\protector_dll.Protector.1
[-] Key deleted: HKLM\SOFTWARE\Classes\protector_dll.ProtectorBho
[-] Key deleted: HKLM\SOFTWARE\Classes\protector_dll.ProtectorBho.1
[-] Key deleted: HKLM\SOFTWARE\Classes\protector_dll.ProtectorLib
[-] Key deleted: HKLM\SOFTWARE\Classes\protector_dll.ProtectorLib.1
[#] Key deleted on reboot: [x64] HKLM\SOFTWARE\Classes\protector_dll.Protector
[#] Key deleted on reboot: [x64] HKLM\SOFTWARE\Classes\protector_dll.Protector.1
[#] Key deleted on reboot: [x64] HKLM\SOFTWARE\Classes\protector_dll.ProtectorBho
[#] Key deleted on reboot: [x64] HKLM\SOFTWARE\Classes\protector_dll.ProtectorBho.1
[#] Key deleted on reboot: [x64] HKLM\SOFTWARE\Classes\protector_dll.ProtectorLib
[#] Key deleted on reboot: [x64] HKLM\SOFTWARE\Classes\protector_dll.ProtectorLib.1
[-] Key deleted: HKLM\SOFTWARE\Classes\AppID\{D616A4A2-7B38-4DBC-9093-6FE7A4A21B17}
[-] Key deleted: HKCU\Software\Classes\CLSID\{BEBBC426-4F16-4567-8FE1-BE198C982027}
[-] Key deleted: HKLM\SOFTWARE\Classes\CLSID\{1AA60054-57D9-4F99-9A55-D0FBFBE7ECD3}
[-] Key deleted: HKLM\SOFTWARE\Classes\CLSID\{25A3A431-30BB-47C8-AD6A-E1063801134F}
[-] Key deleted: HKLM\SOFTWARE\Classes\Interface\{4E6354DE-9115-4AEE-BD21-C46C3E8A49DB}
[-] Key deleted: HKLM\SOFTWARE\Classes\Interface\{FC073BDA-C115-4A1D-9DF9-9B5C461482E5}
[-] Key deleted: HKLM\SOFTWARE\Classes\TypeLib\{A2D733A7-73B0-4C6B-B0C7-06A432950B66}
[-] Key deleted: HKCU\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{25A3A431-30BB-47C8-AD6A-E1063801134F}
[-] Key deleted: HKCU\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{9522B3FB-7A2B-4646-8AF6-36E7F593073C}
[-] Key deleted: HKCU\Software\Microsoft\Windows\CurrentVersion\Ext\Settings\{25A3A431-30BB-47C8-AD6A-E1063801134F}
[-] Key deleted: HKLM\SOFTWARE\Microsoft\Internet Explorer\ActiveX Compatibility\{9522B3FB-7A2B-4646-8AF6-36E7F593073C}
[-] Value deleted: HKLM\SOFTWARE\Microsoft\Internet Explorer\Toolbar [{25A3A431-30BB-47C8-AD6A-E1063801134F}]
[-] Key deleted: HKU\S-1-5-21-4006354873-3992141560-2727822222-1001\Software\InstallCore
[#] Key deleted on reboot: HKCU\Software\InstallCore
[-] Key deleted: HKLM\SOFTWARE\InstallCore
[#] Key deleted on reboot: [x64] HKCU\Software\InstallCore
[-] Key deleted: HKU\S-1-5-21-4006354873-3992141560-2727822222-1001\Software\Microsoft\Internet Explorer\SearchScopes\{AFBCB7E0-F91A-4951-9F31-58FEE57A25C4}
[-] Data restored: HKU\S-1-5-21-4006354873-3992141560-2727822222-1001\Software\Microsoft\Internet Explorer\SearchScopes [DefaultScope] {0633EE93-D776-472f-A0FF-E1416B8B2E3A}
[#] Key deleted on reboot: HKCU\Software\Microsoft\Internet Explorer\SearchScopes\{AFBCB7E0-F91A-4951-9F31-58FEE57A25C4}
[-] Data restored: HKCU\Software\Microsoft\Internet Explorer\SearchScopes [DefaultScope] {0633EE93-D776-472f-A0FF-E1416B8B2E3A}
[#] Key deleted on reboot: [x64] HKCU\Software\Microsoft\Internet Explorer\SearchScopes\{AFBCB7E0-F91A-4951-9F31-58FEE57A25C4}
[-] Data restored: [x64] HKCU\Software\Microsoft\Internet Explorer\SearchScopes [DefaultScope] {0633EE93-D776-472f-A0FF-E1416B8B2E3A}
[-] Key deleted: HKCU\Software\Microsoft\Internet Explorer\LowRegistry\DOMStorage\staticimgfarm.com
[-] Key deleted: HKCU\Software\Microsoft\Internet Explorer\LowRegistry\DOMStorage\ttdetect.staticimgfarm.com
[#] Key deleted on reboot: [x64] HKCU\Software\Microsoft\Internet Explorer\LowRegistry\DOMStorage\staticimgfarm.com
[#] Key deleted on reboot: [x64] HKCU\Software\Microsoft\Internet Explorer\LowRegistry\DOMStorage\ttdetect.staticimgfarm.com
***** [ Web browsers ] *****
[-] [C:\Users\drbruce\AppData\Local\Google\Chrome\User Data\Default\Web data] [Search Provider] Deleted: aol.com
[-] [C:\Users\drbruce\AppData\Local\Google\Chrome\User Data\Default\Web data] [Search Provider] Deleted: ask.com
[-] [C:\Users\drbruce\AppData\Local\Google\Chrome\User Data\Default\Web data] [Search Provider] Deleted: mysearchdial.com
[-] [C:\Users\drbruce\AppData\Local\Google\Chrome\User Data\Default\Web data] [Search Provider] Deleted: start.mysearchdial.com
[-] [C:\Users\drbruce\AppData\Local\Google\Chrome\User Data\Default] [extension] Deleted: abfmigjiaapipflmopkaaooigcjjdojh
[-] [C:\Users\drbruce\AppData\Local\Google\Chrome\User Data\Default] [extension] Deleted: iagcajndpnfncplednpbnkahadegklfa
[-] [C:\Users\drbruce\AppData\Local\Google\Chrome\User Data\Default] [extension] Deleted: jpmbfleldcgkldadpdinhjjopdfpjfjp
*************************
:: "Tracing" keys deleted
:: Winsock settings cleared
*************************
C:\AdwCleaner\AdwCleaner[C0].txt - [5288 Bytes] - [07/03/2017 09:55:26]
C:\AdwCleaner\AdwCleaner[S0].txt - [5225 Bytes] - [07/03/2017 09:50:47]
########## EOF - C:\AdwCleaner\AdwCleaner[C0].txt - [5434 Bytes] ##########
|
|